For all of us, security has become a critical consideration for how we operate online. From organisations that manage customer data, to individuals who have increasingly large digital footprints, everyone has a responsibility to protect their data and we expect others to do the same.
At MongoDB, security is foundational to the way we build our open source database. With over 9 million downloads and hundreds of thousands of production deployments, we are committed to enabling our users to provide security for everyone.
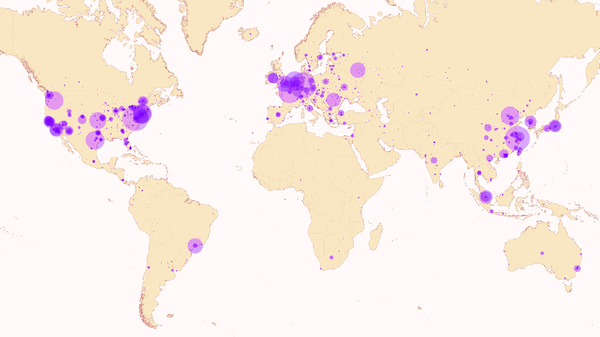
Recently, Information Age reported on research by German students that discovered instances of MongoDB running openly on the internet.
>See also: Major security alert as 40,000 MongoDB databases left unsecured on the internet
As the researchers observed in their report, there is no security issue with MongoDB. Nevertheless, this is an important opportunity for everyone to ensure they are following security best practices.
We have been unable to confirm the claims made in the report, but are doing everything we can to help users evaluate their deployments and apply restrictive measures. If users have a concern about their MongoDB deployment please contact support@mongodb.com.
When to secure access
Security by its very nature imposes restrictions. Therefore, as with any technology, security and convenience can be at odds with one another.
Without oversimplifying this complicated issue, consider your smartphone. When you first set up your phone with all your personal data, you choose whether to add a passcode. Perhaps you never enabled this feature (you should!), or you used your phone for some time before taking this precaution. Most would agree – using a passcode makes using your smartphone more secure but less convenient, and that’s the right tradeoff for anyone with important data at risk.
In many ways it’s the same with application development: early in the project, safely behind a firewall, access control may be disabled to simplify development. When moving the application from development into the public domain, access control should be carefully evaluated to meet the requirements of the organisation.
These requirements of course vary, but in most cases they limit access to authenticated users, and prevent the type of access on the open internet described in the report. Clearly in some cases some applications did not take this crucial precaution.
Security requires a comprehensive approach to system design. We believe holistic security architecture must cover the following: user rights management to restrict access to sensitive data, implemented through authentication and authorisation controls; operations logged against the system in an audit trail; encryption of data in motion over the network and at rest in persistent storage; and environmental and process controls.
MongoDB works with partners and experts across industries, including financial services and government agencies, to provide extensive features for securing database access, including controls for authentication, authorisation, auditing and encryption. We provide documentation about security, such as configuring MongoDB for secure access and protecting access at different levels, as well as a checklist to help ensure deployments are secure.
>See also: Cloudera and MongoDB join forces to power modern application development
Open and transparent
Like many successful software companies, MongoDB is open source and that’s incredibly important to us. We are committed to our community and their contributions. Being open source also means that anyone can download the product and deploy it however they want.
For instance, our most popular installer – RPM – creates a process that limits access to localhost, which would mitigate the issue raised by the researchers. We also provide other options with more flexibility, allowing users to deploy in configurations that are less restrictive.