Hundreds of millions of users of the social media site Tumblr have had their details advertised for sale on the darknet, just weeks after it was revealed that professional networking site LinkedIn suffered a similar breach.
In both cases, the logins were stolen several years ago but only recently came to light: more than 167 LinkedIn IDs were stolen in 2012 and were discovered last month posted in a Russian hacker forum.
> See also: 117 million LinkedIn users' data up for sale over Darknet
According to Motherboard, who was tipped off by security researcher Troy Hunt, the data dump found on the darknet contained 65,469,298 unique emails and passwords.
However, unlike LinkedIn's data, the the passwords were 'hashed' and 'salted' – techniques that turn the actual passwords into a string of digits, making them very hard for hackers to crack.
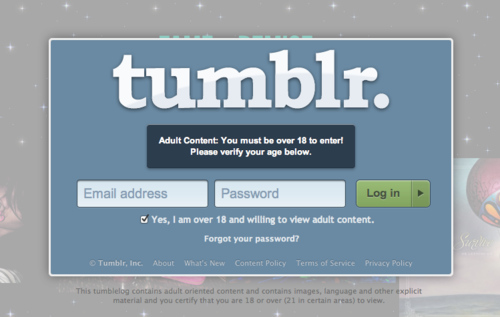
'We recently learned that a third party had obtained access to a set of Tumblr user email addresses with salted and hashed passwords from early 2013, prior to the acquisition of Tumblr by Yahoo,' wrote Tumblr on a blog post.
The Tumblr breach is now listed on Have I Been Pwned as the third largest dump of stolen customer information ever, behind Adobe and LinkedIn.
'Personally identifiable information is a high value commodity for hackers; anything that helps to build a complete picture of a person can be far more valuable than credit card numbers,' said Matt Middleton-Leal, regional director, UK & Ireland at security specialist CyberArk.
'So the ability for hackers to use the leaked emails to tease out more information about individuals via phishing techniques is the concern, as other areas of their digital lives may then be at risk. Many of our online account passwords are the same or similar, so learning which one opens up other doors will be their chosen tactic.'
> See also: What next? How to prevent the consequences of a data breach
For organisations that handle large amounts of user data, their legal ability to ‘sit on’ historical mega breaches is set to disappear under the new EU General Data Protection Regulation.
'This means the onus is on them to enforce best practice so, if or when they are breached, data lost or compromised is able to be contained,' added Middleton-Leal. 'Real-time monitoring and analysis of user behaviour that gives firms a fighting chance of spotting an attacker when there is an infiltration attempt is what’s needed.'