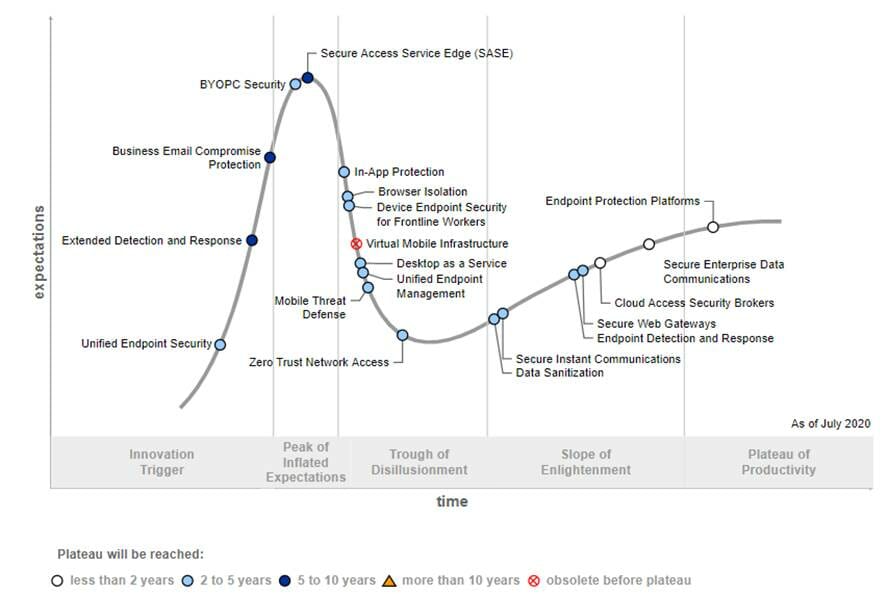
The Gartner forecast features BYOPC security and secure access service edge (SASE) as two technologies that are expected to reach mainstream adoption in the near future.
Security for BYOPC, an endpoint deployment strategy that allows employees to run applications and access company services using personally selected and purchased devices, is expected to be a mainstream concept in the next two to five years.
This emerging strategy has made it necessary for CISOs and security leaders to implement specific security practices accordingly.
What working from home means for CISOs
SASE, however, could take five to 10 years to reach mainstream adoption within businesses, according to Gartner. The technology allows any endpoint to access any application over any network in a protected manner, and delivers multiple capabilities such as SD-WAN, secure web gateways, cloud access security broker (CASB), next-generation firewall and zero trust network access (ZTNA).
The 2020 Hype Cycle for Endpoint Security saw BYOPC security and SASE reach the Peak of Inflated Expectations.
“Prior to the Covid-19 pandemic, there was little interest in BYOPC,” said Rob Smith, senior research director at Gartner. “At the start of the pandemic, organisations simply had no other alternative.
“The urgent need to enable employees to work from home and a lack of available hardware bolstered its adoption globally. Gartner clients said their adoption of BYOPC is up from less than 5% in 2019.”
“CISOs and security leaders should expect the need to support BYOPC to be dependent upon a long-term work-from-home strategy, and also expect to support security tools needed for a BYOPC environment.They need to prioritise their security practices, including enabling multifactor authentication (MFA) for all access to any corporate resource regardless if virtual or not, and if cloud or on-premises.
“Organisations must contain all cloud application data and disallow local storage or upload of local data from any BYOPC device as this could infect the cloud system. They also need to virtualise access to any traditional on-premises application.”
In addition, as BYOPCs are often more vulnerable to malware, ransomware and phishing, IT departments need to limit and control access by offsetting the PC hardware investment with critical security technologies such as multi-factor authentication (MFA), CASB, ZTNA, virtual desktop infrastructure, and desktop as a service.
Specops study reveals biggest remote working cyber security concerns
Study reveals the biggest cyber security concerns regarding remote working among senior staff.
Gartner analysts are set to explore security trends further at the Virtual Security & Risk Management Summit for EMEA and the Americas, from the 14th-17th September 2020.






