There is a market problem that only data-centric security and homomorphic encryption can solve.
In the first six months of the year, there were 4.1 billion records exposed by data breaches, and this has risen to approximately six-and-a-half billion since then. Data breaches are becoming more frequent and damaging.
This failure to solve the growing security crisis is crippling the confidence of large enterprises in their ambition to move to the cloud, which can be a risky, but necessary venture.
Why is it necessary? The legacy implications of not moving to the cloud are affecting data. Data remains the number one underutilised corporate asset, “which is unacceptable in this data-driven environment,” explained AJ Jennings, founder and CEO at ShieldIO, the specialist in real-time homomorphic encryption — we’ll come to that later.
Working on legacy frameworks is exacerbating the enterprises’ inability to view and gain valuable insights from encrypted data without decrypting it (data exposure), as is disruptive regulatory data compliance restraints. KeyStores are a continuing vulnerability and outdated data protection methodologies, databases and applications leave infrastructures stressed and dissatisfied.
There are a number of stress factors affecting data protection, including; regulated data compliance requirements, exponential growth of PII, PHI and PCI data, the requirement for the monetisation of dark data, a consistent barrage of external malicious attacks and accidental or internal malcontents and cloud migration demand vs cloud security.
To address the above problems, a data-centric approach is needed in the security landscape. IT security requires a blanket of protection from perimeter to network; physical to application, anti-malware to policy management and training.
A challenging war on many fronts: combating cyber attacks with a data-centric defence
Real-time homomorphic encryption
Real-time homomorphic encryption — the ability to perform mathematical functions on data and get search queries back without decrypting it — is a solution that fosters a data-centric approach to security.
With this technology, where ShieldIO is a pioneer, “privileged and non-privileged users can get value from the encrypted data in real-time, without seeing, exposing or decrypting the actual data,” said Jennings.
The company’s solution can be deployed as a standard JDBC, OBDC, .NET and EF database driver. It sits next to these existing databases and this eliminates the latency issues associated with encrypted data and the complexities of deployment — to examine encrypted data used to take too much compute power.
There is faith in this product as Oracle, and a number of other cloud service and large database providers, are bringing ShieldIO into its cloud ecosystem, to help customers in their moves to the cloud.

Who should be responsible for a company’s encryption keys?
Removing the KeyStore
Eliminating the vulnerability of the KeyStore — the repository of security certificates — is fundamental to reducing the available attack footprint of a hacker.
“Hackers steal encryption keys, they very rarely break the encryption,” said Simon Bain, CTO, ShieldIO. “KeyStores are vulnerable because someone hasn’t taken enough notice of their data and secured it correctly, because they haven’t looked at the value of that data.
“Data is king and money, and people need to be trained to appreciate this. They need to look at how that data is stored and what’s vulnerable — organisations think if they go to AWS it will be fine, which is what Capital One did, and it was breached.”
How does ShieldIO overcome this problem? According to Jennings, the solution encrypts down to the database subfield level, utilising standard AES-256 encryption. “We then generate ephemeral keys for each encrypted bit utilising our propriety AI algorithms at random cryptographic combinations.” The key is then destroyed, which eliminates the ability for a hacker to access decrypted data by stealing the KeyStore.
Use cases
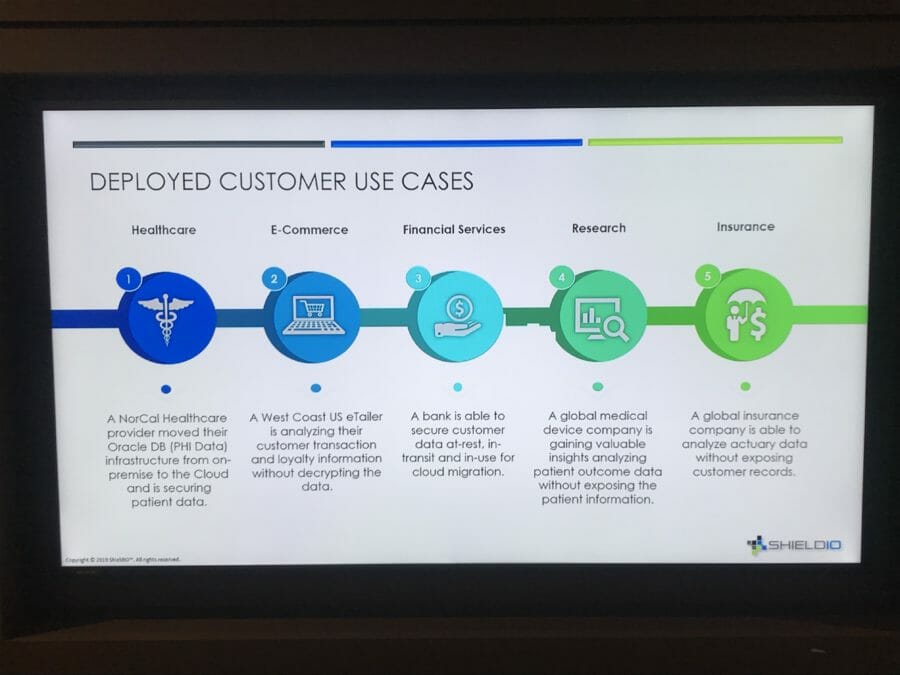
When moving from on-premise to cloud migration, security is an issue. “ShieldIO has acted as a catalyst to helping Oracle move its customers to the cloud, securely, across several verticals,” continued Jennings.
Make security easy
Users need to do their job, but it’s important that blockers don’t get in the way, in the name of security. Security needs to be efficient, but it should run in the background and not interfere with users doing their job.
“Our job is to make security as easy and secure as possible and not get in the way of people’s jobs,” confirmed Jennings.
This can be achieved by enabling; access to encrypted data in-use, development test environments to use real data without exposing live data, real-time speed of query on a fully encrypted dataset and, a simple, fast and transparent data security implementation through standard database drivers.
*Bain explained that the regulation coming into play is a “kneejerk reaction by governments. It is needed, but isn’t responding to the problem,” he said. “On the face of it, the regulations look good, but actually it’s not — they don’t understand the situation. They don’t like big tech companies in the US and regulations like the CCPA are impacting the consumer negatively. Regulation needs to be there, but governments need to look at the ecosystem more carefully — it shouldn’t be politicians designing it.”
Related articles
The comprehensive IT security guide for CIOs and CTOs v
The current state of the cyber security industry: it’s a mess
UK CTOs, CIOs and CISOs have confidence in security, despite growing threats
Using AI intelligently in cyber security







