After last week’s WannaCry outbreak, ransomware is no longer an unknown subject to anyone in technology circles. The malware that often comes in via email (though WannaCry did not), locks up a business’ data until a ransom is paid has become so commonplace over the past two to three years that people outside the technology world know what it is.
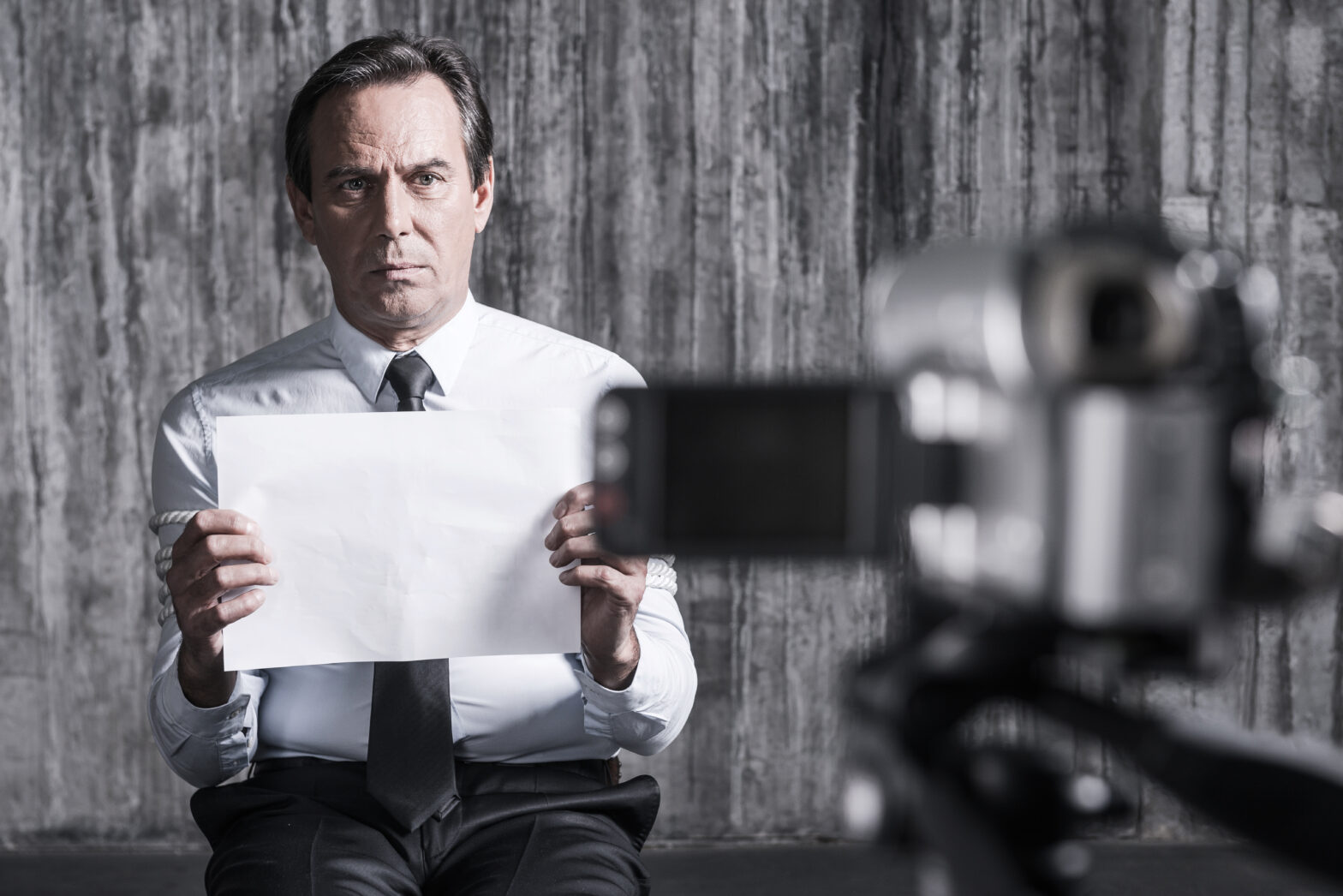
WannaCry – which is still stealing headlines at the time of this writing – brought the topic of ransomware screaming to the forefront of our collective consciousness. These attacks are fast, often happen without the users’ knowledge and can do massive damage to a company’s finances, productivity or brand. When users become locked out of their systems, they have to revert to doing business the old-fashioned way – with a pen and paper, which affects productivity and revenue.
>See also: NHS Trust successfully fought back WannaCry ransomware with AI
One thing is certain: ransomware has become a “when, not if” scenario for businesses of all sizes. To pay or not to pay is ultimately a business decision, and one which most organisations do not make lightly.
Pay up? How to decide
Whether they are tax files, intellectual property or sensitive HR information, ransomware gains access to files your business cares about and can be extremely harmful. Any business can find itself in the firing line of this growing type of internet extortion, here’s some guidance on when to pay up and when to hold out.
When to pay:
1. Poor backups: Unknown to the IT team, your company’s backups (if it does automatic backups) have been failing for weeks or the restore features have never been tested and actually don’t work.
In a survey conducted by KnowBe4, when faced with this scenario, 57 percent of IT experts would pay the ransom and hope for the best for a business.
>See also: Ransomware: the new highway robbery
2. Removal isn’t working: the IT team has tried, but that problematic ransomware just doesn’t want to move. If the lost files are critical to the business’ success – or the management’s peace of mind – then paying becomes a real option.
3. Too much time: Ransomware can shut down business operations; car manufacturer, Renault, for instance, was hit by WannaCry and was forced into stoppages at several of its production sites. If the downtime a business faces is likely to have a critical impact on the company’s success, or cost more than the ransom itself, paying the ransom might be worthwhile.
4. Can’t recreate: if the company is faced with significant lost work that will be difficult, if not impossible, to recreate.
When NOT to pay:
1. Good working order: The business has a good working backup.
2. Isolation: IT has isolated the infection to one machine and it has not invaded or shut down other computers on the network.
3. Security pro’s: there is a top-notch cyber security team in place that knows exactly which ransomware family and version infected the business and can unlock the data.
>See also: North Korea linked to global ransomware cyber attack
4. No long term impact: If the business can afford the downtime or the loss of data, opting to pass on the ransom can work in its favor. This often depends on the size of the organisation (large enterprises are unlikely to find themselves in this position).
5. Personal choice: It’s a matter of principle for the leadership and no amount of damage makes it worth paying the ransom.
No money transfer. This is bitcoin territory
If the organisation has decided to pay the ransom it might not be as easy as simply transferring the money.
Bitcoin, ransomware’s preferred payment method because it’s not backed by any central bank and can often be used without being linked to an identity, is tricky stuff. KnowBe4 has helped dozens In their desperation to get hijacked files back it is often necessary to for businesses and consumers to call upon the help who already have bitcoin accounts to pay the ransom for them. Why? Because setting up a bitcoin account takes up to four days, and when victims are facing a deadline of less than a week it is the only answer.
>See also: The global ransomware attack a cyber wake-up call
It would be wise for businesses to investigate and get familiar with what it takes to set up a Bitcoin wallet so they are prepared to move should ransomware hit.
Moving forward – prevention
The big question now is how to move forward to prevent ransomware. Ransomware usually enters an organisation via an email – unassuming users click on a bad link or open an email attachment that looked legitimate but that included malicious code. Businesses should employ a defence-in-depth strategy to prevent that double-click from costing the business big time:
• Start with a weapons-grade backup and test it regularly to see if the file-restore function really works.
• Organisations should run antivirus software but not rely on it. Today’s antivirus usually does not catch all ransomware.
• Update, update, update. IT teams need to make sure all software is up-to-date. That means the Windows software, and any other software running on a computer.
>See also: Next-generation technology to relieve the pain of hospital bed shortage
• All users should have different passwords for different systems. By setting up a password manager, users can use one master key, rather than remembering every password, and increase the company’s security posture.
Ultimately, an organisation’s users is its last line of defence. In addition to the work the IT team does, businesses should train their users to think before they click, confirm that emails and fishy attachments are really from a trusted source and ask for IT’s help if they think something seems strange or off base. Oh, and don’t’ forget to remind users when they see those special offers come into their email: if it looks too good to be true, it probably is.
Sourced by Stu Sjouwerman, CEO at KnowBe4