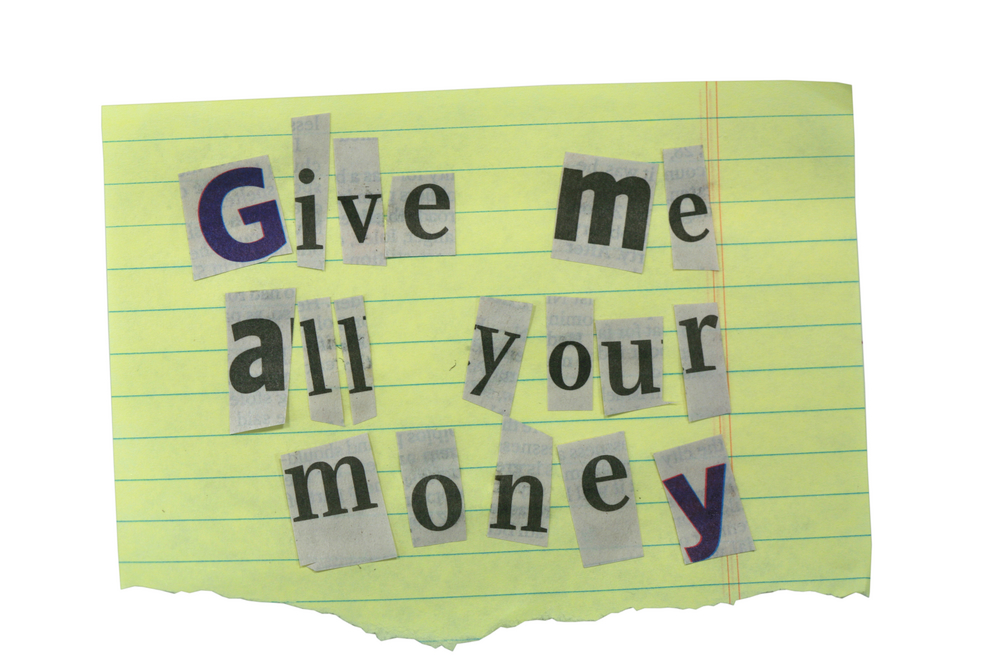
In the last few years ransomware – malware that encrypts a user's data or freezes their device in order to extort money from them – has risen seemingly out of nowhere to become one of the greatest cyber threats facing organisations around the world. But how has it become such a widespread problem?
A new report released today by enterprise security firm Palo Alto Networks looks into how ransomware has become such an effective way for cyber criminals to make money, and what the future looks like for these kinds of attacks.
Ransomware spans the globe, is indescriminate about its victims, and there is no negotiating with it as it executes in a matter of seconds to leave organisations and their computers on lockdown.
In recent years, there has been a 600% increase in the number of ransomware families, with strains like Locky, Teslacrypt and the first ransomware to target OS X, KeRanger, making news.
> See also: How to make your data immune to ransomware
Following the launch of Bitcoin in 2013, which allowed users to easily and anonymously exchange money in the form of digital currency, there are now 30 malware families active around the world.
The success of ransomware is down to its highly lucrative business model, as Palo Alto Networks has revealed.
Attackers have spent many years trying to perfect this business model, and now a perfect storm of factors have made it a golden era for those that profit off ransomware.
Traditionally, hackers profited by stealing data and selling it on underground markets. But the price for stolen records has plummeted in recently years falling from $25 per record to only $6 per record has necessitated new sources of income for cyber attackers, with many of them turning to ransomware as typically, the returns are far higher (often several hundred dollars upwards).
And while ransomware campaigns are extremely complex to carry out due to the technology involved, the cost for the attacker is relatively low.
So what does the future hold?
Advances in attack distribution, anonymous payment methods such as cryptocurrencies, and the technology to reliably encrypt and decrypt data, have all helped criminals rake in the cash.
The explosion of IoT (Internet of Things) devices will mean that the concept of ransomware will become even more widespread as attackers will be able to hold a number of integral devices to ransom. As Palo Alto Networks explains, a device like a connected refrigerator, while containing no sensitive data, could have its cooling mechanism disabled by a clever enough attacker until the user pays up, rendering it useless.
We can expect higher ransoms, as attackers figure out how to hone in on systems with the most valuable information and increase their ransoms accordingly.
And ransomware is likely to become highly targeted, by criminals who are able to first infiltrate an organisation's network to pick and choose the most highly valuable data.
'Until organisations around the world adopt a prevention mindset, and stop paying ransoms to retrieve their data, this criminal scheme will continue to threaten all Internet-connected devices,' says Palo Alto Networks.
To change this dynamic we have to move beyond the current attack or campaign to identify and block the underlying architecture, therefore cutting criminal activity off at the source.
> See also: The rise of ransomware 2.0 – how to fend off the new school of ransomware
'As ransomware attacks act quickly – typically within minutes of an infection – the 'detect and respond' model provides little value in limiting their impact,' says the report. 'If a detection system alerts you that an infection has occurred, it’s very likely already too late to stop your files from being encrypted. It is critical to deploy controls that are able to prevent malware from entering the network and executing on the systems storing your valuable data.'
The majority of new ransomware uses strong cryptography that can't easily be reversed. But if it's too late and you've already become infected, some security vendors have found ways to decrypt files without paying the ransom. To do this, it's vital to first understand what you are dealing with by identifying the family of ransomware.
Paying a ransomnote, advise the experts, should be an absolute last resort, as 'payments help fund criminal enterprises and perpetuate attacks by encouraging others to hold more data for ransom,' helping to keep the lucrative business of ransomware a viable business model for opportunist criminals.