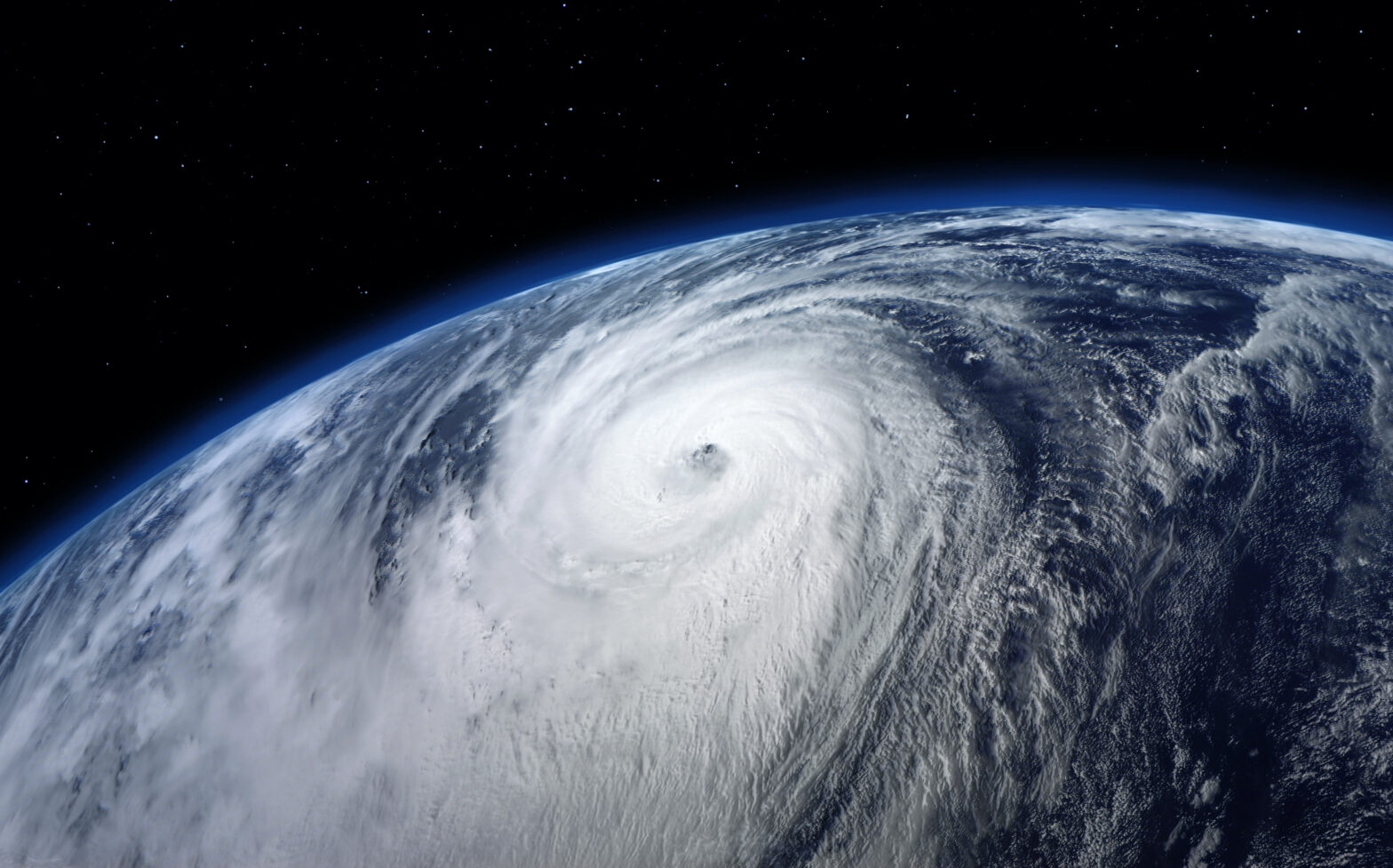
Hurricanes, much like there namesake, represent those attacks you can see coming and, for the same reason, earthquakes are those you can’t.
Both are inevitable, and organisations need to plan and take action accordingly. This starts with an understanding of what threat intelligence is and how to make it relevant and actionable.
The key is being prepared for both the foreseeable attacks as well as the ones that sneak up on you. This is where threat intelligence comes in, helping your organisation transition from constantly just reacting to threats to become more proactive in its approach. Threat Intel allows you to prepare for the hurricanes and respond to the earthquakes with an efficient, integrated approach.
Eliminate noise
Mention threat intelligence and most organisations think about multiple data feeds to which they subscribe — commercial sources, open source, and additional feeds from security vendors — each in a different format and most without any context to allow for prioritisation.
>See also: The value of sharing threat intelligence
This global threat data gives some insight into activities happening outside of your enterprise; not only the attacks themselves, but also how attackers are operating and infiltrating networks.
The challenge is that most organisations suffer from data overload. Without the tools and insights to automatically sift through mountains of disparate global data and aggregate it for analysts and action, this threat data becomes noise; you have alerts around attacks that aren’t contextualised, relevant, or a priority.
To make more effective use of this data, it must be aggregated in one manageable location and translated into a uniform format so that you can automatically get rid of the noise and focus on what’s important.
Focus on threats
With global threat data organised, you can focus on the hurricanes and earthquakes that threaten your organisation. Hurricanes are the threats which you know about, can prepare for, protect against and, anticipate based on past trends.
For example, based on research, say that we know a file is malware. This intelligence should be operationalised; turned into a policy, a rule, or signature and sent to the appropriate sensor so that it can prevent bad actors from stealing valuable data, creating a disruption, or causing damage.
As security operations become more mature, you can start to receive alerts on these known threats in addition to automatically blocking them so that you can learn more about the adversary. This allows you to focus on the attacks that really matter.
Earthquakes are unknown threats, or threats that you may not have adequate countermeasures against, which have bypassed existing defences. Once they’re inside the network, your job is to detect, respond, and recover.
This hinges on the ability to turn global threat data into threat intelligence by enriching that data with internal threat and event data and allowing analysts to collaborate for better decision making.
>See also: What’s next for threat intelligence?
Threat intelligence helps you better scope the campaign once the threat is detected, learn more about the adversary, and understand affected systems and how to best remediate.
By correlating events and associated indicators from inside your environment (e.g., SIEM alerts or case management records) with external data on indicators, adversaries, and their methods, you gain the context to understand the who, what, when, where, why, and how of an attack.
Going a step further, applying context to your business processes and assets helps you assess relevance. Is anything the organisation cares about at risk? If the answer is no, then what you suspected to be a threat is low priority. If the answer is yes, then it’s a threat. Either way, you have the intelligence you need to quickly take action.
Make intelligence actionable
Intelligence has three attributes that help define “actionable.”
Accuracy: Is the intelligence reliable and detailed?
Relevance: Does the intelligence apply to your business or industry?
Timeliness: Is the intelligence being received with enough time to do something?
An old industry joke is that you can only have two of the three, so you need to determine what’s most important to your business. If you need intelligence as fast as possible to deploy to your sensors, then accuracy may suffer and you might expect some false positives.
If the intelligence is accurate and timely, then you may not have been able to conduct thorough analysis to determine if the intelligence is relevant to your business. This could result in expending resources on something that doesn’t present a lot of risk.
Ultimately, the goal is to make threat intelligence actionable. But, actionable is defined by the user. The security operations centre typically looks for IP addresses, domain names, and other indicators of compromise – anything that will help to detect and contain a threat and prevent it in the future.
>See also: Pay attention to your threat intelligence’s shelf life
For the network team, it’s about hardening defences with information on vulnerabilities, signatures, and rules to update firewalls, and patch and vulnerability management systems.
The incident response team needs intelligence about the adversary and the campaigns involved so they can investigate and remediate. And the executive team and board need intelligence about threats in business terms, the financial and operational impact, in order to increase revenue and protect shareholders and the company as a whole.
Analysts must work together and across the organisation to provide the right intelligence in the right format and with the right frequency so that it can be used by multiple teams.
Operationalising threat intelligence will, of course, take time and requires thorough planning.
Many organisations are already beginning to move from a reactive mode to become more proactive. But, in order to make time to look out at the horizon and see and prepare for hurricanes while also dealing with earthquakes, organisations need to move to an anticipatory model with contextual intelligence, relevance, and visibility into trends in the threat landscape.
Sourced by Jonathan Couch, senior vice president, strategy, ThreatQuotient