The driving force behind the favourable adoption of push to accept authentication is its ease of use, which greatly increases user acceptance and training, traditionally two of the biggest hurdles to implementing a security solution.
While push to accept does make it easier for users to authenticate, it also provides a new path for attackers to circumvent an organisation’s second factor protection.
>See also: Is multi-factor authentication finally picking up speed?
The technology uses an idea that has been present in computing for many years, and as such inherits the downsides of that methodology.
How can an attacker circumvent push to accept?
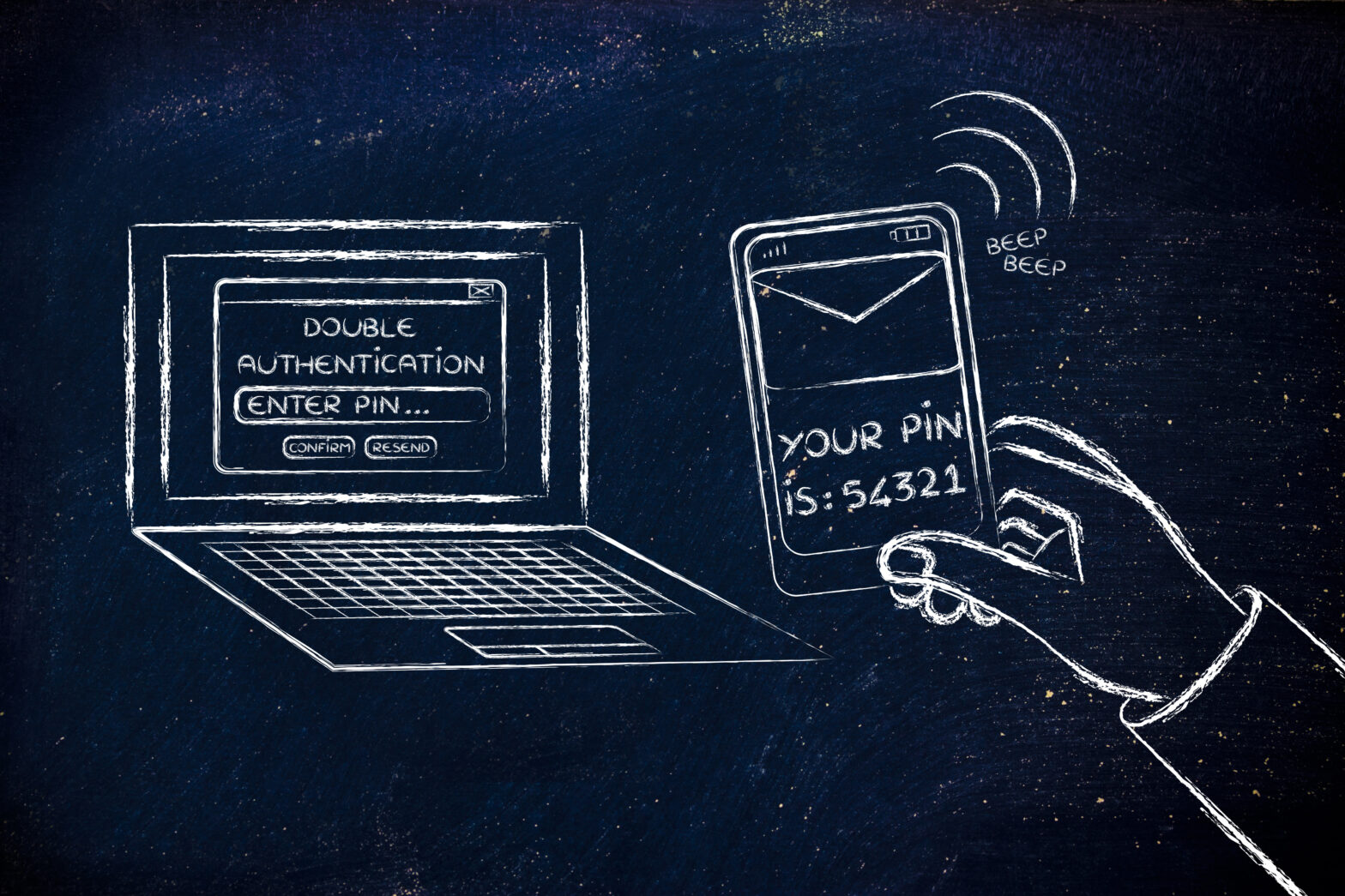
- An attacker attempts accessing the target corporation’s systems.
- Using stolen credentials the attacker logs-in to a secure application as a legitimate employee.
- The authentication solution sends the employee a push to accept prompt, they push ‘accept’, thereby agreeing to the access request.
- The attacker has obtained access to the corporation’s secured system.
The scenario is surprising to most people because the employee has tapped “Allow” in the dialog even though they were not logging in at the time. No one would do this in real life, would they? Unfortunately, yes. The reason behind that decision is based on how the human brain responds to stimulus, such as the push to accept prompt.
Research by scientists from Brigham Young University, The University of Pittsburgh, and Google, using an MRI, measured a human brain’s dramatic drop in attention that results when a user is shown just two security warnings in a short period of time. The official term for this effect is called “habituation”.
What this means is if an attacker triggers a few push to accept requests, in a short period of time, a user will likely not read the prompt and just click accept to dismiss the dialog to make the requests go away.
This effect has been noted by David Kennedy of TrustedSec at his DefCon presentation. He discusses how, when performing Pen Tests for customers, users always tapped allow granting him access.
>See also: Is voice recognition to become part of enterprise authentication?
In every Pen Test engagement where push to accept was deployed, he was able to gain access every time.
As a result, while the use of push to accept has exploded due to its simplicity and speed, it exposes enterprises to risks when users may inadvertently approve login requests that they did not initiate. This could allow an attacker to bypass the intended protection of multi-factor authentication and breach the user’s account.
The technology is arguably one of the most convenient forms of multi-factor authentication but to satisfy today’s changing enterprise landscape, it’s essential for security solutions to evolve at the pace of new emerging threats as well as meeting practical organisational needs.
Some organisations are already moving to stronger methods of user authentication, including adaptive access control techniques safeguarding critical areas, such as single sign-on (SSO) portals and self-service password reset applications.
It is imperative that more organisations take this lead and look to implement adaptive access in a way that performs risk-analysis as part of the authentication process.
Luckily there are solutions out there that can help address the habituation issue but keep the ease of use that makes push to accept so popular.
One such way is with symbol to accept, a patent-pending technology. This starts with a push message to the user’s mobile device but instead of a single accept button, they are presented with several accept buttons.
Each button displays a randomly selected symbol, to successfully log in, a user must select the symbol which matches the on-screen display. This choice dramatically reduces the likelihood that the user will approve an unsolicited login request as they will not know which button to choose if they are not currently trying to log in.
>See also: How to create an IT security strategy that balances defence with offence
The method closes the security gaps caused by habituation, enabling security-conscious enterprises to deploy mobile push authentication with confidence to mitigate risk, while at the same time their user experience is unhindered.
Improving security without compromising convenience is paramount and every organisation must look to take a multi-layered approach to authentication.
Other such techniques include device recognition, geo-location, the use of threat services, and even behavioural biometrics. All of which enable organisations to take control of their authentication process and gain employee adoption at the same time.
Sourced by Ryan Terp, snfo security systems analyst at SecureAuth