With Covid-19 forcing millions of employees to work remotely, the use video conferencing software has soared. Some reports estimate daily users have quadrupled as a result of the crisis.
In response, cybercriminals are targeting the ever-growing number of Zoom users through sophisticated schemes, like phishing. These schemes include the use of social phishing and fraudulent websites set up to steal money from Zoom users who believe they are buying a subscription from Zoom directly. Criminals are also trying to steal Zoom user details to compromise accounts or infiltrate sensitive calls.
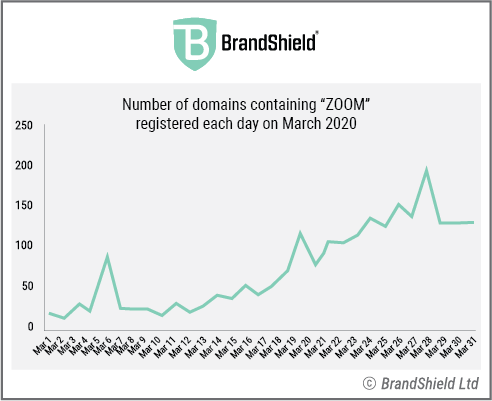
BrandShield‘s online threat hunting system has detected the registration of over 3,300 new domain names containing the word “Zoom” since the beginning of 2020. Of these, over 2200 were registered in March alone. This increase coincided with the spread of the coronavirus and the shift to remote working. Over 30% of these new websites have activated an email server which is an indication of these sites being used to process phishing attacks.
Here are a few examples of suspicious websites detected by BrandShield:
• www.zoomnow.net
• www.zoomus.top
• www.zoomus.net
• www.zoomus.org
• www.zoomus.cn
• www.zoomcallonline.com (possible malware)
• www.zoomroom.link (possible malware)
How to make your Zoom meetings private and secure
Companies at risk
As well as targeting companies through Zoom, cybercriminals are trying different cyber scams to trick companies. These scams include impersonation on social media platforms or phishing emails.
The scams are aimed at tricking employees into giving money away, provide the credentials to cloud-based applications, or pay fake invoices. This increase in online fraud is a significant threat that most companies are not prepared for.
Yoav Keren, CEO, BrandShield, said: “With global businesses big and small become increasingly reliant on video conferencing facilities like Zoom, sadly, cybercriminals are trying to capitalise. Businesses need to educate their employees quickly about the risks they may face, and what to look out for. The cost of successful phishing attacks is bad for a company’s balance sheet in the best of times, but at the moment it could be fatal.
“BrandShield protects some of the biggest corporations in the world and we takedown thousands of threats across websites and social media. We are getting companies approaching us all the time asking for our help. This problem is only going to get bigger as people spend more time transacting and interacting online.”
Will an increase in remote working lead to more cyber attacks?
The coronavirus crisis: an opportunity for cybercriminals
Since the coronavirus crisis began, there has been a surge in fraudulent online activity, with key sectors being targeted including pharmaceuticals, medical supplies, banking, foreign exchange, loan providers, entertainment, online gaming and delivery companies.
According to BrandShield, some of the biggest threats are cybercriminals who are trying to capitalise on fears around the disease, and in many cases using the identities of known companies or brands to trick worried consumers. Attacks have included phishing sites, social phishing, fraudulent ecommerce sites, and fake medicine.
BrandShield has outlined the following simple steps companies and employees should take when to handle the growing online threat:
1. Monitor — always monitor the digital sphere to find any fraud related to your company or brands, quickly
2. Enforce fast — make sure you respond fast and effectively to take down fake sites and fake social media users or posts.
3. Educate — and warn your employees and customers – proactively communicate to highlight the dangers.
4. Manage and control — manage a complete online threat intelligence map, prioritise the potential threats, control reactions and monitor their results.
5. Be proactive — Finding vulnerabilities and securing your weak spots. For example, remove old company websites that might be used for fraud.
[emailsignup]







