Messaging giant WhatsApp has announced that all its content is now fully encrypted by default.
The move follows the weeks-long battle between Apple and the FBI over the right to access encrypted content on a terror suspect's iPhone. Now WhatsApp has made its own stance on encryption clear by creating a system that makes it impossible for court-authorised search warrants to be carried out on its users' data.
This new addition to WhatsApp's security features means that all content shared between its billion plus users, including voice calls, videos and group chats across all phone and operating systems are now covered by end-to-end encryption.
With one billion users around the globe, WhatsApp is second only in size to its parent company, Facebook.
> See also: An insecure platform: WhatsApp can read user’s ‘secure’ messages
'While WhatsApp is among the few communication platforms to build full end-to-end encryption that is on by default for everything you do, we expect that it will ultimately represent the future of personal communication,' said company founders Jan Koum and Brian Acton in a blog post.
'The desire to protect people's private communication is one of the core beliefs we have at WhatsApp, and for me, it's personal,' added Koum. 'I grew up in the USSR during communist rule and the fact that people couldn't speak freely is one of the reasons my family moved to the United States.'
In March the messaging service’s encryption stymied a court-approved wiretap after upgrading its security in 2014. But now it has switched on full encryption for all its customers around the world.
The encryption system is thanks to a partnership with Open Whisper Systems, a nonprofit software group endorsed by Edward Snowden, whose protocols ensure all encryption keys are stored locally, so cannot be accessed even by WhatsApp's own servers.
Open Whisper Systems' mission is to make end-to-end encryption commonplace and simple, offering its SMS, messaging and call encryption tools for free. It also wants to get other instant messenger applications to follow suit.
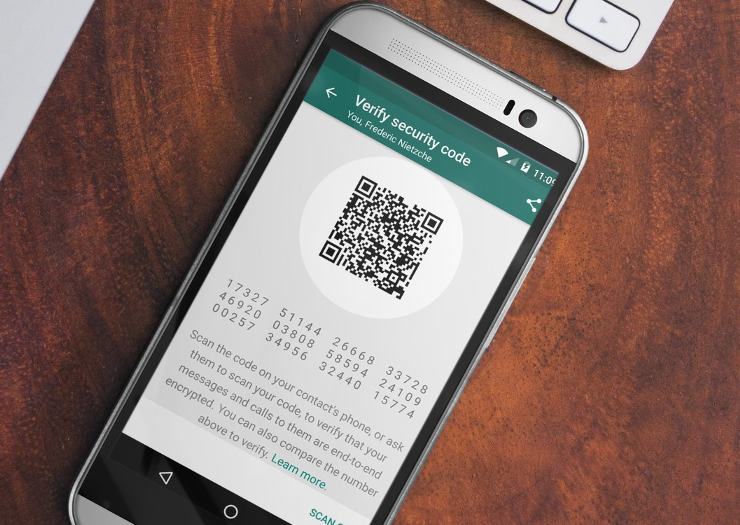
As of today, users will be informed when they send a WhatsApp message that all calls and chats are secured with end-to-end-encryption. Users can then can scan a QR code on their contact's phone which verifies the authenticity of their encrypted session.
It's a great leap for the messaging giant towards securing users data, as well as making them more aware of the privacy of their communications.
Tony Pepper, CEO of Egress Software Technologies, argues that as consumers gain a better sense of control over their privacy, many will expect higher levels of security in the workplace as a result.
This big win for privacy advocates could create challenges, however, for organisations looking to retain control over their sensitive data – so what does it mean for the future of Bring Your Own Device and Bring Your Own App schemes?
> See also: Researchers break a hole in Apple's 'unbreakable' encryption
'It’s good news for security in general that consumer technologies, likeWhatsApp, are offering end-to-end encryption,' said Pepper. 'The more encryption becomes ‘the norm’, the less resistance IT will have in getting people to adopt it in a commercial environment.'
The fact that end-to-end encryption is now being offered in popular apps means that employees will expect, and even push to have, the same level of information security from the data sharing tools they use for work, such as email and online collaboration.
'This could help to create a safer data sharing environment for everyone', said Pepper.
'However, I still have concerns when it comes to using these apps within a commercial environment,' he added. 'While ‘bring your own app’ (BYOA) is very suitable in some circumstances, consumer-grade technology does not provide the same level of assurances demanded by the work environment.'
'If staff start using such technology at work, employers will still have no way of knowing what information is being shared or how it is being used, and will ultimate fail to protect sensitive customer data. As such, it could cause more problems than it solves.'
But encryption alone is only part of the battle in the enterprise – being able to audit, track and control the lifecycle of data as it is shared is equally important.
Pepper advises that organisations make sure the tools they give to employees are usable as well as secure to avoid them defaulting to personal devices, while also retaining control to ensure sensitive information doesn’t find its way to public platforms or unintended third parties.