The need to hunt for cyber threats has never been so important, particularly following serious attacks such as that on an NHS Trust which shut down routine operations and appointments for three hospitals, as well as the huge breach of names, email addresses, telephone numbers, dates of birth and encrypted passwords at Yahoo!
Data breaches were prominent last year and this distressing trend has continued in the same vein at the beginning of 2017.
It has become evident that it is not a matter of if an organisation experiences a cyber attack, but a question of when. In the case of Yahoo, malicious code marauded within its network for nearly 3 years, exposing up to one billion users.
Now, simply having a firewall at the gate to the ‘data kingdom’ is no longer enough due to the amount of malicious traffic directed towards it.
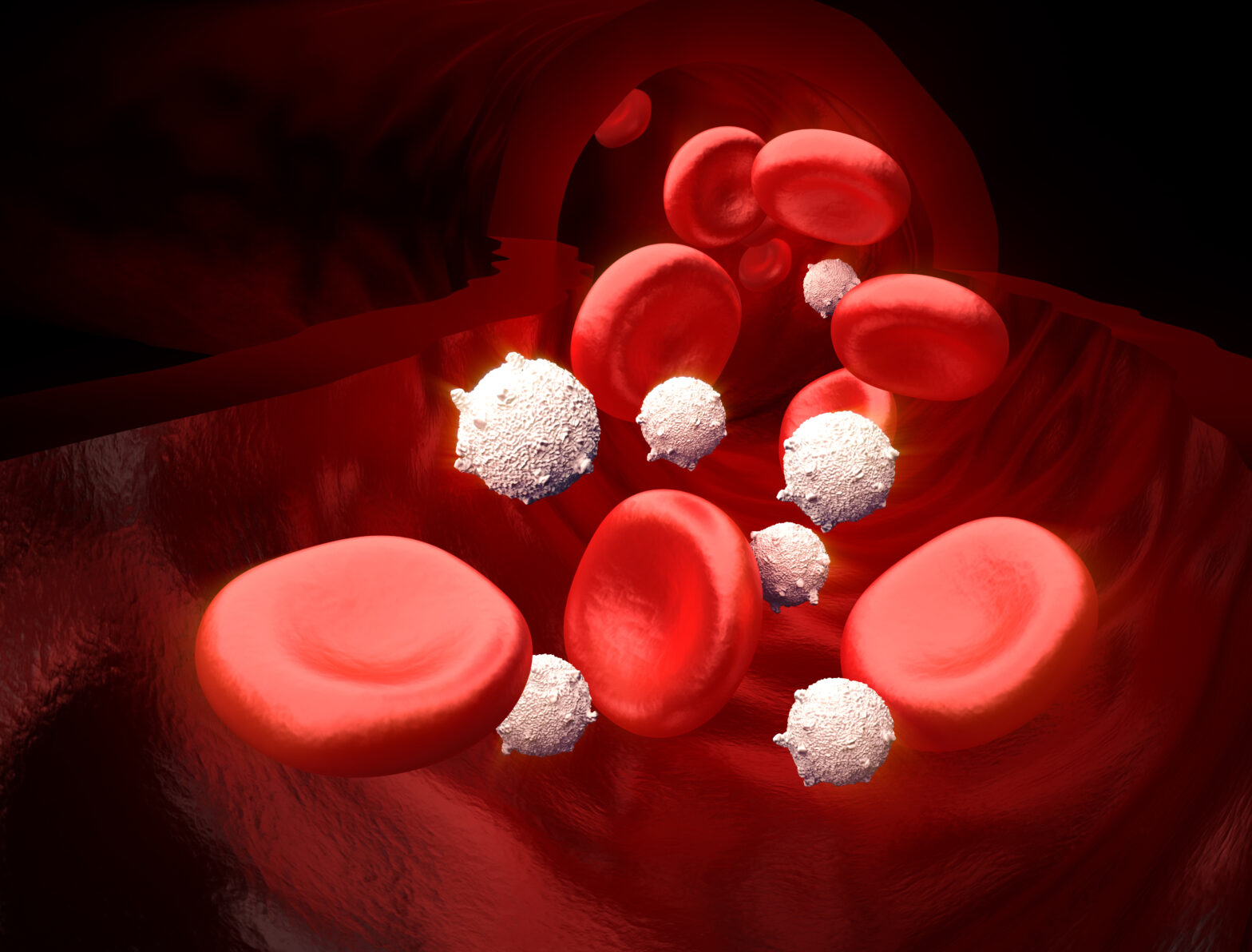
Something will get in, and therefore, it is imperative to have security protocols equivalent to white blood cells in the human body: monitoring and detecting what gets through the initial perimeter.
>See also: Prevention, detection and incident response: the cyber security industry
Andy Bushby, UK sales director at Fidelis Cybersecurity, discussed with Information Age the importance of an effective monitoring security system. A system that can dig as deep as the attackers hide within an organisation’s network.
In the interview, Bushby made clear that not enough was being done by potentially vulnerable organisations to detect and remove threats from their networks and endpoints. But why do organisations find this so difficult? Is it an attitude problem from the top?
Bushby told Information Age that “the reason organisations find it very hard once these threats are inside is that traditionally organisation’s monitor on the ingress or egress from the network. I think it’s more important for people to start thinking about ‘east west’ monitoring. This refers to the monitoring of the inside of the network and understanding what is normal and what is maybe abnormal in that respect. Crucially, if you aren’t looking for something it is very easy not to see it.”
“There has to be better monitoring of that traffic,” Bushby continued. “The other thing organisations aren’t looking at is what is happening on their endpoints. If you’re not monitoring your traffic internally the other way to do it is to look at what is happening on the end machines, what code is running on those.”
“Organisations might have an anti virus or a firewall on those endpoints but that is normally as far as it goes. Some may have data loss prevention (DLP). Looking at data loss prevention from the endpoint is a start, but they are not looking at what is actually happening: what applications are being run, or what network connections are being made from those endpoints. It’s very easy to miss this if you’re not looking for it.”

From this it is evident that organisations are vulnerable on two fronts. If the firewall or border is breached and effective monitoring/detection solutions are not in position internally or at the endpoint then a significant issue arises.
So how can this be addressed within an organisation, where does the direction, the change in strategy need to come from? Presumably it is a boardroom issue and a top-down approach is needed.
“The boardroom is starting to pay attention,” stated Bushby. “The strategies from the UK government, in particular, and the Cabinet Office have emphasised cyber security’s importance.”
>See also: How to prevent the most dangerous cyber threat: insider attacks
“They have told boardrooms they need to be more involved and that they need to care about cyber security in the same way they do health and safety. I believe they are starting to look at it now in that respect.”
But Bushby emphasised that the boardroom must be aware that a change of tactics is required. “It needs to be a case of them being aware of the strategies that are being used. Not the technical details, but the overall high level strategy. I think we should see more non executive members on boards that have an understanding of technology. We should probably also see the CISO either as a guaranteed attendee at every board meeting or even starting to see them properly on the board of these organisations. This will help change the attitude, but also produce the right strategy.”
With EU GDPR on the horizon it is certainly in the board’s interest to protect their data, as from May 2018 a breach will be significantly more expensive for an organisation to pay. To give some context, TalkTalk’s £400,000 fine post-GDPR would look more like £60 million.
“It will start to change their appetite,” said Bushby. “This new legislation has very real financial consequences. The risk means it’s of the level that the board will care about it. The fines will be significant and they will affect the big bottom line of the organisation.”
Research analysts from Gartner suggest a complete, all-in-one, security solution is required to survive in the connected age.
As mentioned previously, however, even the most effective security solutions can be vulnerable (this may not always be the case with artificial intelligence set to shake up the security scene in the next two to ten years). Bushby agreed and mentioned that “I don’t think there is a magic button. Something will always get in.”
>See also: What next? How to prevent the consequences of a data breach
What will stand the best current solutions out, is having the capability of identifying the breach once inside the system and dealing with it appropriately and swiftly.
It’s a brave new world, but “if you want to work in it”, concludes Bushby, “we have to be connected to the internet, we have to be communicating. It is a risk we have to take. But in doing so, we must make sure that we are as secure as possible”.