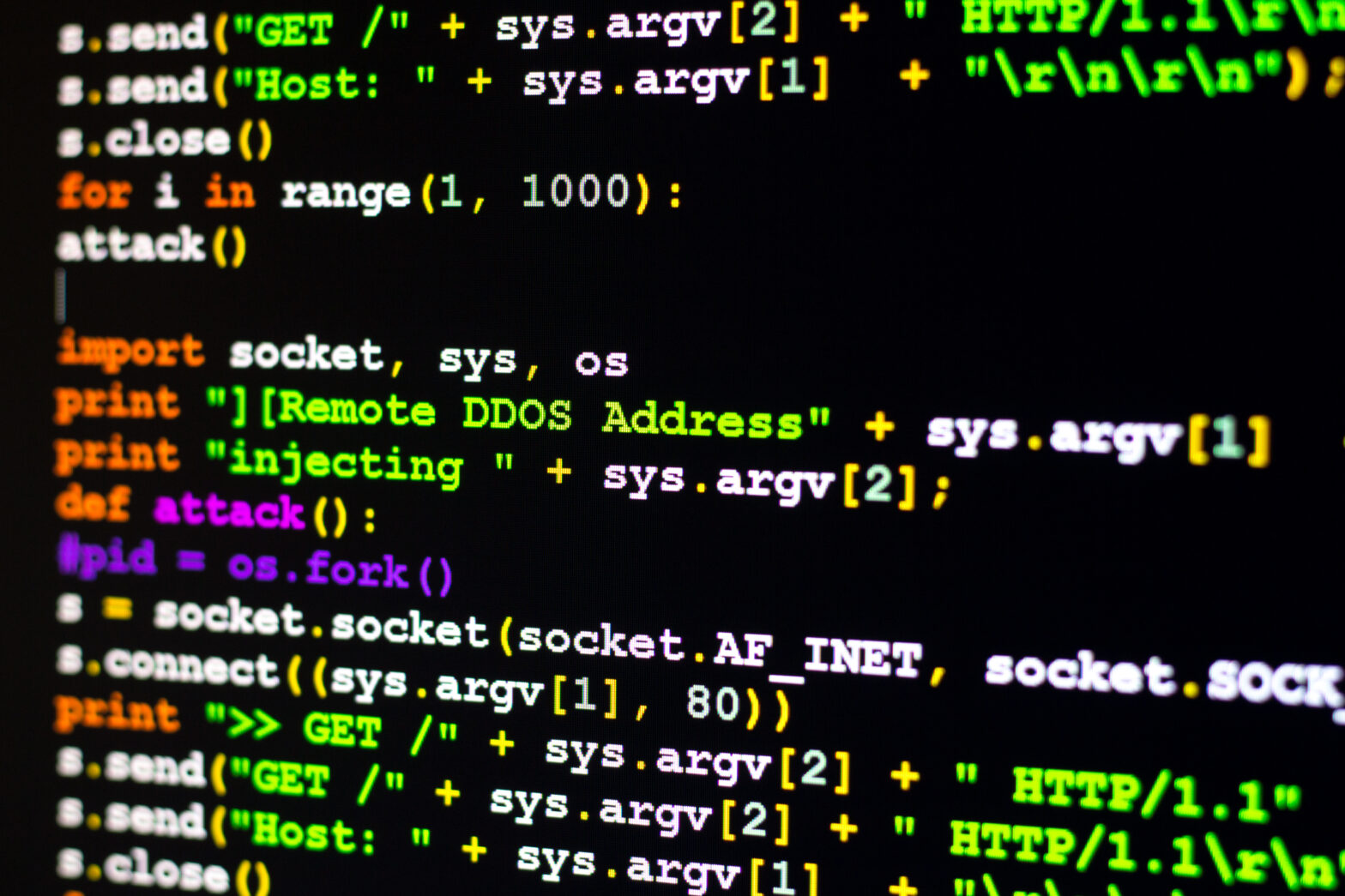
A distributed denial-of-service (DDoS) attack is one of the most popular tools in the cybercriminal arsenal. The motives behind such attacks can vary, from cyber-vandalism to extortion.
In many cases, criminal groups threaten their victims with a DDoS attack unless the latter pay them money (in bitcoins, for example). But sometimes a DDoS attack is used to distract IT staff while another cybercrime, such as data theft or malware injection, is carried out.
Society’s growing dependence on technology in recent years has fuelled the growth of illegal – and profitable – businesses, including fully-fledged ‘as-a-service’ C2C (criminal-to-criminal) offerings.
There are services available on the black market that enable an attacker to launch a (DDoS) attack, for as little as £5 an hour – while the targeted company can end up losing thousands, if not millions, of pounds.
>See also: The effectiveness of standards in preventing and mitigating DDoS
The level of service involved when arranging a DDoS attack on the black market is not very different from that of a legal business. The only difference is that there’s no direct contact between the provider and the customer.
The ‘service providers’ offer a convenient site where their ‘customers’, after registering, can select the service they need, pay for it, and receive a report about the attacks. In some cases, there are even customer loyalty programmes, with clients receiving rewards or bonus points for each attack they buy.
There are several factors that affect the cost for the customer. One is the infrastructure used. For example, a botnet of 1,000 surveillance cameras may be cheaper than a botnet of 100 servers. This is because cameras and other IoT devices are currently less secure – a fact that is often ignored by their owners. However, not all those providing attack services are ready to specify such details.
Another factor is the duration of the attack (measured in seconds, hours and days), and the client’s location. DDoS attacks on English-language websites, for example, are usually more expensive than similar attacks on Russian-language sites.
Another big factor affecting the cost is the type of victim. Attacks on government websites and resources protected by dedicated anti-DDoS solutions are much more expensive, as the former are high risk, while the latter are more difficult to attack.
>See also: DDoS attacks are an increasing concern for IT security pros
For instance, on one DDoS-as-a-service website, the cost of an attack on an unprotected website ranges from £35 to £80, while an attack on a protected site costs £370 or more. If the target uses traffic filtering systems to protect its resources, the cybercriminals have to come up with ways of trying to bypass them to ensure an effective attack, and this also means an increase in the price.
According to Kaspersky Lab research, a DDoS attack can cost anything from £3 for a 300-second attack, to £370 for 24 hours, with the average price for an attack being around £20 per hour. Kaspersky Lab’s experts were also able to calculate that an attack using a cloud-based botnet of 1,000 desktops is likely to cost the providers about £5 per hour. That means the cybercriminals organising DDoS attacks are making a profit of around £15 per hour.
Some services offer a choice of attack approaches, which allows cyber criminals to combine different scenarios and perform attacks tailored to the individual characteristics of the victim. For example, if the victim successfully combats a SYN-flood attack, the attacker can switch the scenario on the control panel and evaluate the victim’s reaction.
The attack scenario that offers greatest profitability for cybercriminals involves the attackers demanding a ransom from a target in return for not launching a DDoS attack, for calling off an ongoing attack. In fact, those carrying out the blackmail don’t even need to have the resources to launch an attack – sometimes the mere threat is enough.
The growing profitability of DDoS attacks will see hackers increasingly using it to extort, disrupt and mask other more intrusive attacks on businesses. Worryingly, small and medium sized businesses are not confident in their knowledge of how to combat these threats effectively.
>See also: Brexit negotiations could be disrupted by DDoS attacks
The longest DDoS attack in 2016 lasted 292 hours (about 12 days) according to Kaspersky Lab’s research. Most online businesses can’t-afford to have their ‘doors closed’ for even an hour, let alone for 292 hours, as criminals take advantage of their poor defences. Companies that host these online sites are also under attack on a daily basis.
The clients of these services understand perfectly well the benefits of DDoS attacks and how effective they can be. The cost of a five-minute attack on a large online store is about £3. The victim, however, can lose far more because potential customers simply cannot place an order. We can only guess how many customers an online store loses if an attack lasts the whole day.
At the same time, cybercriminals continue to actively seek new and cheaper ways to organise botnets. In this regard, the Internet of things makes life easier for them. One of the current trends is the infection of IoT devices (CCTV cameras, DVR-systems, “smart” household appliances, etc.) and their subsequent use in DDoS attacks. Since many are vulnerable to attack, cybercriminals are able to exploit them easily.
>See also: Major French news sites victim of DDoS attack
It should be noted that DDoS attacks, particularly ransomware DDoS, have already turned into a high-margin business: the profitability of one attack can exceed 95%. And the fact that the owners of online sites are often willing to pay a ransom without even checking whether the attackers can actually carry out an attack (something that other fraudsters have already picked up on) adds even more fuel to the fire.
The average cost of DDoS attacks in the near future will only fall, while their frequency will increase. This is why it’s essential to deploy a solution that protects against all types of DDoS attack, regardless of their complexity, power, duration and the specific systems they target.
Sourced by David Emm, principal security researcher, Kaspersky Lab