TalkTalk’s recent data breach is the latest in a long line of security incidents that have compromised the sensitive details of hundreds of millions of users.
Similar incidents at LinkedIn, Sony, and Yahoo, are amongst the dozens of other hacks that together have put billions of accounts at risk.
In order to address the issue of cyber security, companies often advise users to select complex, unique passwords for each account and recommend changing them frequently.
However, the majority of consumers tend to reuse old passwords or choose weak ones, in spite of the risk this poses.
In fact, “123456” and “password” have topped SplashData’s annual “Worst Password” report as the most commonly used passwords – 5 years in a row.
>See also: Is voice recognition to become part of enterprise authentication
Security experts have known for some time that usernames and passwords alone aren’t enough to protect users.
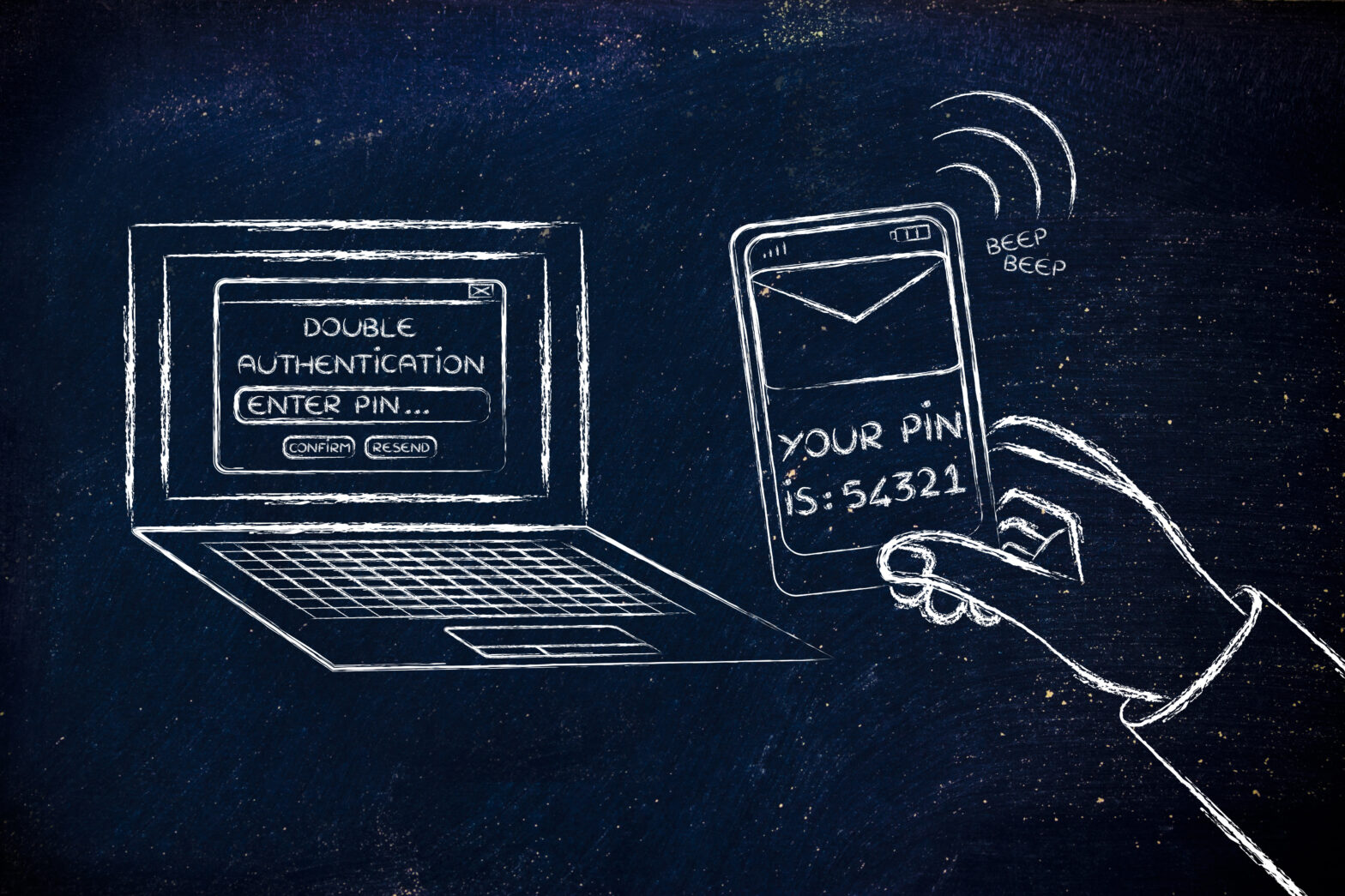
The industry is beginning to recognise the importance of added security, namely two-factor authentication (2FA).
More reliable than familiar knowledge-based methods of security (username, password, pin, security questions, etc.), 2FA hardens account security by requiring customers to provide a code that is transmitted to their device, which is something they own.
Your mobile device is a far more secure form of authentication compared to your mother’s maiden name, your date of birth, or another piece of information that someone could potentially attain.
One would assume that every online service would have implemented 2FA at this point.
Unfortunately, you need only spend a few minutes on TwoFactorAuth.org to see how many services have yet to adopt better security.
The struggle between UX and good security
The online industry is in an ongoing battle to devise strong security measures that consumers will actually use.
In a recent study, Microsoft researchers found that no alternative security method is as easy to use, or implement, as passwords.
They wrote, “Marginal gains are often not sufficient to reach the activation energy necessary to overcome significant transition costs, going on to say that the ‘funeral procession for passwords’ is likely still many, many years out.
>See also: Is multi-factor authentication finally picking up speed?
Adding extra steps to the log-in process ultimately frustrates the user, sometimes to the point of discontinuing the service and causing security fatigue.
For this reason, businesses have traditionally shied away from clunkier – though stronger – security in order to preserve the user experience.
For example, take SMS, the most popular form of accomplishing 2FA.
Users log on to a site, are prompted to send an SMS verification code to their phone number, and then are asked to enter the code into the website.
This is still preferable to just a username and password, but in an era where businesses focus on converting as many website visitors as possible, adding extra steps to the user journey can seem counterproductive.
With any security measure it’s always a question of stakes. SMS shouldn’t be the security gateway to high-risk information, such as bank accounts or medical records.
But there’s no reason to avoid using the efficient and convenient SMS for low-risk communications that have little to no risk associated: a text to notify users that a car has arrived; an appointment reminder from their dentist; or a code to set up a mobile app.
Where do we go from here?
Luckily, the security industry never sleeps. In the past 18 months, a new form of 2FA has emerged, based on a technology we use and interact with on a regular basis: push notifications.
Unlike SMS, which by default is unencrypted, push notifications can start a chain of end-to-end encrypted communications between the app and a secured authentication service, thus providing “Push authentication”.
Push authentication sends a notification directly to your device over the internet.
Simply responding to the push initialises secure software that then displays an intended message to the device owner.
>See also: Why you should be prioritising cyber security risk management
But instead of just a string of random numbers, push notifications can include context in an authentication request. For example:
“Would you like to authorise this transfer for $1,000 to Ima Thief?”
“An attempt to access your account originated in Antarctica. Is this you?”
Reactive fraud alerts only alert the victim to the illicit action, but a push notification empowers the user to respond immediately and prevent the attack.
Whilst there is still a place for SMS authentication and text-delivered codes, such as in locations where broadband access is either unreliable or expensive, generally we should all be considering utilising push notification in authentication scenarios.
Push is familiar and easy to use for consumers, and the technology is mature and reliable.
Pushing passwords out of the picture
Over the past year, new forms of push authentication have been integrated into the services of popular consumer sites.
Yahoo, Google, Microsoft, and even online gaming giant, Blizzard, are rolling out “password-less” experiences, powered by push.
While this is a huge win for users, these solutions are specific to the individual communities served by each of these companies and their products, and don’t present an adoption strategy for businesses looking to develop something similar.
>See also: How to implement a secure defence from hackers
Fortunately, we live in an age of readily available, flexible building blocks for software development that can scale and keep up with increasing customer demands and changing business needs.
Today, there are more and more APIs disrupting formerly-monolithic industries: infrastructure, payments, communications, and even account security.
What’s more, companies like live-streaming service Twitch and virtualisation leader VMware understand the importance of securing user accounts – that’s why they looked to cloud-driven, reliable two-factor authentication layers to further protect their communities.
In your migration to agile, cloud-based development, don’t leave the safety of your customers behind.
Sourced by Marc Boroditsky, VP & general manager of authentication at Twilio