The current cyber security landscape is one of confusion, but also one of recognition that things need to change.
This is best demonstrated in the government’s introduction of initiatives, such as Cyber Essentials. But, even this is under review and it is unclear what that will be moving to in early 2020 — more confusion!
In the face of a cyber security crisis, there’s a huge amount of certifications, accreditations and models out there that organisations are advised or even, compelled to adopt.
The pinnacle of these is ISO 27001 — the only information security management system standard that can be independently certified with a level of authority. Even NIST Cyber Security does not have that ‘certification’ so it’s another reason why smarter and more powerful buyers are pushing for ISO 27001
On top of this, the regulatory landscape is catching up with things like the updated Data Protection Act and the GDPR.
The comprehensive IT security guide for CIOs and CTOs
https://www.youtube.com/watch?v=xDk6vWExTtA&feature=youtu.be
“Doing nothing is not an option”
Leaders and businesses are starting to recognise that “doing nothing is not an option” but they’re unsure on what to do, according to Mark Darby, founder of Alliantist, the company behind ISMS.online — which helps organisations demonstrate that they can be trusted for information security management.
Why the change of heart? Darby points to the increasing risks and consequences of suffering a breach as the main reason. And, because of this and regulations like GDPR, much larger organisations — the powerful ones in the supply chain, who can dictate to their suppliers what they do — are seeking recognised certification.
“The easiest one is perhaps Cyber Essentials, but that only goes so far,” says Darby. “A better, more recognised one by smarter organisations that want to see physical security as well as cyber security and secure product development, instead of just router protection and so on, is ISO 27001.”
This new way of approaching security is still emerging and the landscape is still fractured and confused.
“Somebody needs to drive a bit more of a wedge through it to make it easier for organisations that are starting to recognise that they’re consciously incompetent, instead of unconsciously incompetent,” he continues.
Tech Nation’s cyber security cohort: ISMS.online company profile
Moving from unconscious to conscious to proactive
Admitting the problem in cyber security is the first step. Then it’s a case of proactively addressing the security gap in an organisation.
Embracing Cyber Essentials is a good start, but as Darby has alluded to, it’s not enough.
“What, hopefully, the likes of the UK’s National Cyber Security Centre (NCSC) and others will do is that they’ll start to coalesce around a recognised standard, like ISO 27001,” he hopes. “Rather than all these organisations trying to bring their own flavour of something out, it will be far better if there were efforts made to help organisations across key areas.
“I think we will move towards that over the course of time, but what organisations can do themselves is perhaps start to educate their supply chain.”
AI in cyber security: predicting and quantifying the threat
Secure the supply chain
Failures across the supply chain are one of the biggest security hurdles to overcome.
It’s time for organisations to embrace what Darby calls “responsible customer, responsible supplier programmes”.
“Let’s imagine that you are a large bank and you’ve got a very significant supply chain, instead of just sending down that supply chain a contract that says you will achieve ISO 27001, why not help them do it? Why not equip them with the capability to do it? So they’re actually building capacity and capability in their supply chains and making supply chains more resilient? There’s a lot that larger organisations could do to help the smaller, less wealthy, less experienced organisations.”
Collaboration is key. It always has been. But, it’s been frustrated by a natural business reaction to keep best practices or ways of working a secret.
It’s now about embracing a smarter way of working and adopting products that help organisations look up and down their supply chain; find out where are the risks, the consequences and the opportunities, and then look in that base to be saying has anyone already solved these problems and if so, how?
Tech Nation’s cyber security cohort: Corax company profile
Cost challenge
Cyber security skills are a scarce commodity.
And, because of this, specialist prices are going through the roof — which means that it makes the topic of security unaffordable for smaller organisations to achieve; they can’t afford very significant consulting support.
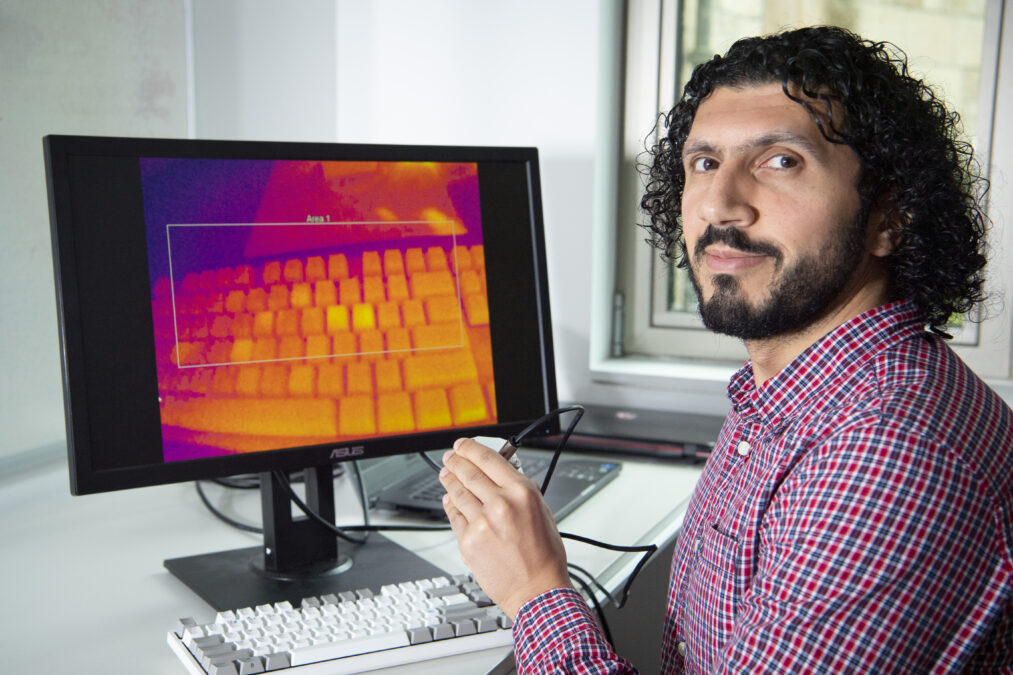
To combat this, Alliantist have asked: “how do we codify scarce resource? How do we start to use automation, machine learning and things like that and build it into a product,” asks Darby?
Organisations will have to be looking at different ways of working to firm up the supply chain. But, crucially, even if they had the money, the resources don’t always exist.
Governments, businesses, universities and other educational establishments are starting to address this talent shortage and build future capacity. But, it doesn’t exist entirely at the moment.
Cyber security and IoT: skills shortage hampering development
Strategise information security
As with most technology-related initiatives, security has got to start from the top; “not least because of the threats and risks around GDPR and loss of valuable IP is a serious issue,” says Darby.
In today’s media-first environment, breach scandals and data misuse are damning; potentially costing organisation’s millions or billions depending on their market cap. Shareholders and wider stakeholders are going to be really cued in as a result.
If an organisation can’t be trusted then it’s not going to go out and win business and it’s not going to strategically be able to grow in the areas that it wants to — a key consideration of those in charge.
Referring to his own background in business and strategy, Darby said: “Information security was affecting my ability to grow, so we had to get inside and understand that, because we were a technology company delivering software services that held valuable data inside them for our customers.
“Anyone who is a data processor on behalf of another organisation, is going to need to demonstrate that they can be trusted, and that’s a board level challenge. So if you’re in a large bank or you’re in a two-person organisation, that’s a significant growth challenge.”
“We couldn’t have grown our organisation without having a strategic approach to information security” — Darby
Leading the cyber security charge
In the largest organisations, the CEO or board is not likely to lead the charge on cyber security.
However, this responsibility will fall on the shoulders of the CIO, CTO or CISO — individuals of that calibre, given the importance of the subject.
“At a strategic level where you’re joining up organisations across the supply chain, and it affects every employee and every supplier, the senior management should handle that,” says Darby.
“In larger organisations, you typically encounter the DPO, the CISO, the CTO, the CIO or a senior level person sponsor,” he continues. “But, in the small to mid-size organisations, you’re talking director level, owner level, founder level.
“It’s a tricky challenge that you can’t delegate to the most junior of people; it needs that level of leadership and engagement.
“Even though it’s not an expensive problem to solve with tools like ours, it’s a remarkably expensive problem when it goes wrong or you fail to win that new business without it.”
Alliantist, the company behind ISMS.online is part of Tech Nation Cyber — the UK’s first national scaleup programme for the cyber security sector. It is aimed at ambitious tech companies ready for growth.