The relationship is not symmetrical. Cyber criminals are highly motivated. “They’re not bound by bureaucracy or normal business rules,” says David Carroll of XQ Cyber, for them cyber crime is a “revenue opportunity to get rich, so you can imagine how fast the wheels are spinning.” By contrast, cyber security is by definition about defence “it’s got bureaucracy wrapped in it.” And that loads the dice in favour of the bad guys, which means the good guys, need all the help that they can get. And that is the first benefit of automation in cyber security.
“These market place sites on the dark web,” says Jeremy Hendy of Skurio… you see “a really nice well designed website, it looks like Amazon or eBay, but the categories down the left are weapons, guns, drugs, data…credit cards…”
How do you grapple with the threats that might emerge from the dark web? For Hendy and the rest of the team at Skurio the solution lies with…yes you guessed it, automation of cyber security.
For Terry Pudwell, Chief Exec of Assuria Limited, there are too few people available with the necessary cyber security skills. “And if you want to employ some security people in your business, it’s going to cost you a fortune.”
For Carroll there is another issue: “the industry almost appears as though it’s deliberately keeping the technology complicated.”
Maybe it is as if the cyber security industry likes to scare or blind potential customers, especially smaller firms, with science. Throw in lots of jargon. Make the problem seem intractable. “some penetration testers show off, make things unnecessarily complex” said Carroll.
IBM says automation is the next big step in cyber security
So what’s the solution?
Terry Pudwell, likens Assuria’s automation of cyber security to a black box on an aircraft which records the actions of pilots, so you learn the errors that occurred, that might have led to a crash and you can then go about fixing them. “And that’s what we’re trying to do in the IT security world.”
He cites an example: “If someone logs on to corporate systems from three o’clock on a Sunday morning, that might be legitimate, it might not be and there’s some judgement needed. We’re trying to stop things happening in realtime. But you definitely need to make sure you know exactly what happened, so you can fix it. So our technology, pulls this information effectively from these black boxes, pulls the log data out, stores it and then analyses it against a set of rules.”
For Skurio, automation has a quite different role. Its technology searches both the dark web as well as ordinary sites which may contain information that a company would like to know about. Each client can then feed in key words: email addresses for example, names of staff, as well as products and then the technology goes out and regularly looks for information “then we’re bringing that information into a database and making it searchable.”
The importance of third-party validation for cyber solutions
It’s the sheer number, though that make automation in this cyber security context applied to the dark web so vital. “We can see 200 thousand password combinations on a usual day. There’s just loads of data swirling around…one of the datasets that was floating around last year had 1.4 billion sets of usernames and passwords…it’s just gigabytes and gigabytes of data.”
It’s not just about the dark web. Hendy gives the example of Cathay Pacific, they apparently accidentally ran a promotion where you could buy first class tickets to anywhere in the world for a ‘ridiculous’ knockdown price. A forum then spotted this, and there was a massive spike in bookings, each one loss-making. Hendy reckons that this is a good example of the kind of information that the Skurio technology would have spotted.
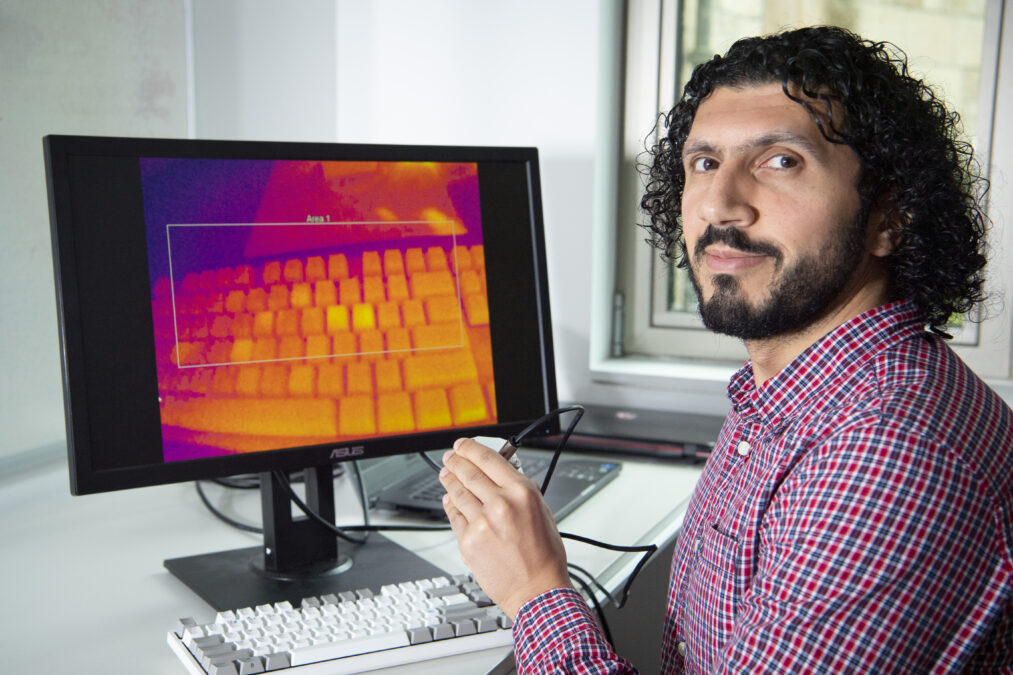
David Carroll says that automation of cyber security also involves a lot of simple English — of ditching jargon. XQ Cyber put together a team of software engineers and penetration testers to develop an engine. “We take all of the raw technical data that you would get from a scan of your network and we interpret it.” The engine can then highlight vulnerabilities that could be something to do with the operating systems, the applications or it could relate to the network. And in plain English we tell the user, this is what we found, these are the potential implications. And this is what should be done about it.”
Carroll speculates that if all NHS hospitals had an automation system of this type in place, then there would have been an awareness of the vulnerabilities in their system in advance of the Wanna Cry attack and the simple patch that would have closed the vulnerability would have been in place.
For Carroll, the ultimate answer to automation of cyber security would be what he calls, slightly in cheek, ‘the big red button.’ “We are somewhat away from the giant red button that says, fix this now,” he says, “that will be the next phase of automation.”
Simulation software: protecting your organisation during a sustained period of cyber war
Advice
So what advice do our three experts have for customers?
Terry Pudwell says “the risks of not doing something are just too high. And imagine if something happens and sensitive information is leaked. And either your business goes down or something terrible happens to some other people. You have no defence in court.” He emphasises the word reasonable — take reasonable cyber security steps, “regulators don’t expect you to spend more on cyber defence than on R&D.”
Carroll says “I would go to the NCSC website and look at the essentials page, there are five things that you should do:
- Secure your Internet connection
- Secure your devices and software
- Control access to your data and services
- Protect from viruses and other malware
- Keep your devices and software up to date
Jeremy Hendy takes a broader perspective. “Any larger organisation has got thousands of different systems, a lot of them moving to the cloud, and, in general, data about customers is being shared with supply chain partners, whether that’s for payment processing, or just data flowing around very complex supply chains.
“When you look at data breeches as an example, many breeches occur as a result of some third party system being compromised.
“It’s not your network that has leaked the data, it’s not your fault. But it’s still ultimately your responsibility.”
XQ Cyber, Skurio and Assuria Limited are part of Tech Nation Cyber — the UK’s first national scaleup programme for the cyber security sector. It is aimed at ambitious tech companies ready for growth.
Related articles
Tech Nation’s cyber security cohort: Skurio’s company profile
Tech Nation’s cyber security cohort: XQ Cyber’s company profile
Tech Nation’s cyber security cohort: Assuria’s company profile
Democratising technology for cyber security and the power of AI
Automation is shaping the future of the workplace