A thermal attack system guessed 93% of eight-symbol passwords and all six-symbol passwords in a study
Computer security experts have developed a system capable of guessing computer and smartphone passwords using thermal imagery.
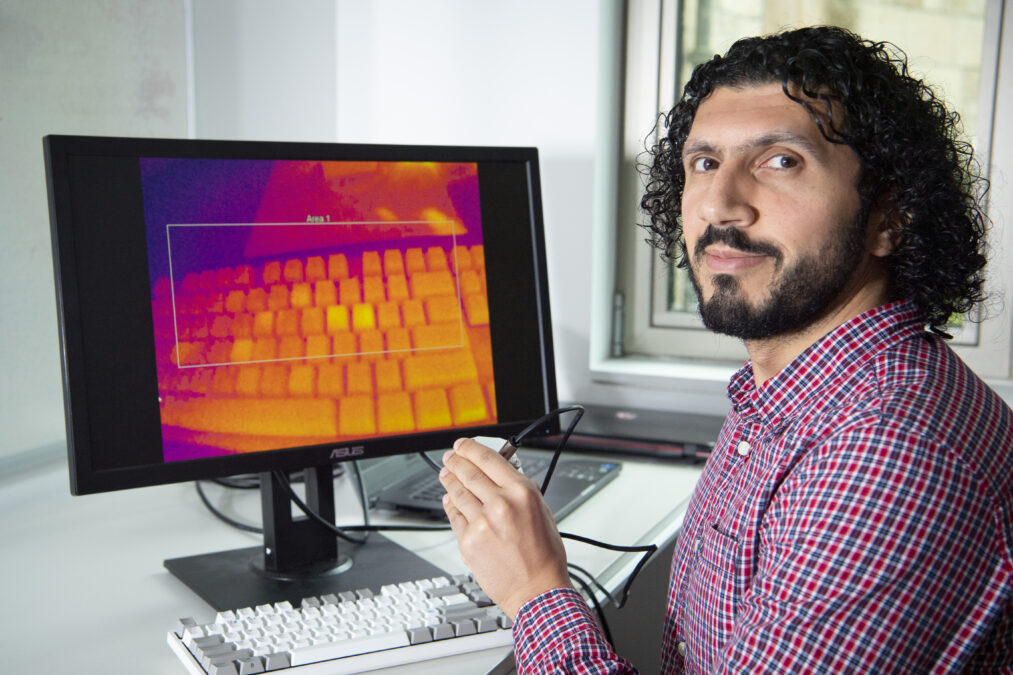
Researchers from the University of Glasgow developed the system called ThermoSecure which analyses the traces of heat fingertips leave on keyboards and screens.
Thermal attacks can occur after users type their passcode on a computer keyboard, smartphone screen or ATM keypad before leaving the device unguarded. A passer-by equipped with a thermal camera can take a picture that reveals where their fingers have touched the device.
The brighter an area appears in the thermal image, the more recently it was touched and therefore the order sequence can be estimated.
Previous research by Dr Mohamed Khamis, who led the development of the system, found that ThermoSecure could reveal 86 per cent of passwords when thermal images are taken within 20 seconds, dropping to 62 per cent after 60 seconds.
They also found that within 20 seconds, ThermoSecure was capable of successfully guessing 67 per cent of long 16-character passwords. As passwords grew shorter, success rates increased – 93 per cent of eight-symbol passwords were cracked and all six-symbol passwords were successfully guessed.
Another aspect which made it easier for ThermoSecure to guess passwords was the typing style of the keyboard users. Users who type slowly tend to leave their fingers on the keys for longer, creating heat which lasts longer than touch typists.
Images taken within 30 seconds allowed ThermoSecure to successfully guess these typists’ passwords 92 per cent of the time and 80 per cent of the time for touch typists.
Keyboard materials also have an effect. ThermoSecure could successfully guess passwords from the heat retained on keycaps made from ABS plastics around half of the time, but only 14 per cent of the time on keys manufactured from PBT plastics.
The research was carried out to demonstrate how falling prices of thermal imaging cameras is making the risk of “thermal attacks” more likely.
Dr Khamis said: “Access to thermal imaging cameras is more affordable than ever – they can be found for less than £200 – and machine learning is becoming increasingly accessible too. That makes it very likely that people around the world are developing systems along similar lines to ThermoSecure in order to steal passwords.”
To stand the best chance of protection against thermal attacks, he added: “Longer passwords are more difficult for ThermoSecure to guess accurately, so we would advise using long passphrases wherever possible. Backlit keyboards also produce more heat, making accurate thermal readings more challenging, so a backlit keyboard with PBT plastics could be inherently more secure.
“Finally, users can help make their devices and keyboards more secure by adopting alternative authentication methods, like fingerprint or facial recognition, which mitigate many of the risks of thermal attack.”
More on cybersecurity
Why bother with ransomware? The rise of ‘low effort’ extortion attacks – Andy Zollo, EMEA regional vice-president at Imperva, discusses the rising threat of ransomware-free extortion attacks on businesses
Who is responsible for cyber security in the enterprise? – Uncertainty is widespread across companies over who takes the lead on cyber security, according to Willis Towers Watson
Use cases for AI and ML in cyber security – We explore how artificial intelligence (AI) and machine learning (ML) can be incorporated into cyber security