Information Age has partnered with Tech Nation to help explore 20 of the UK’s leading cyber security scaleups.
Tech Nation Cyber is the UK’s first national scaleup programme for the cyber security sector. It is aimed at ambitious tech companies ready for growth.
In a series of 20 company profiles, we will be introducing you to the cyber security scaleups that make up Tech Nation’s first cyber cohort.
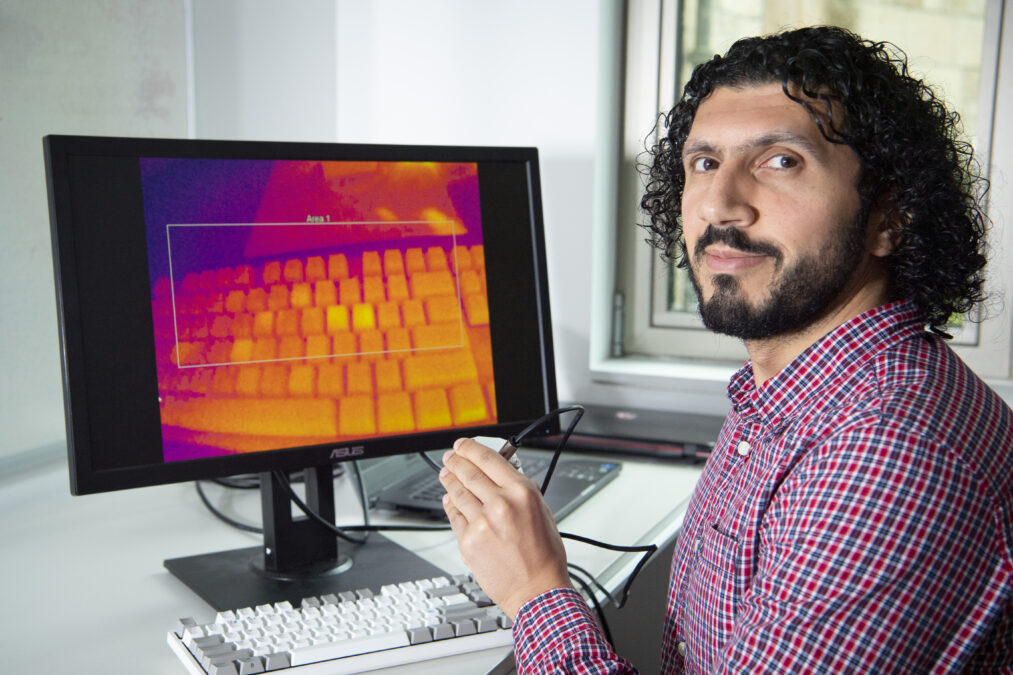
14. Keepnet Labs

All answers provided by James Baker, board advisor at Keepnet Labs
What does your company do?
Our company is a cyber security firm that protects businesses through the life-cycle of email-based attacks.
How do you differentiate to your competitors?
We are different from our competitors because we have produced multiple, multi-layered solutions under one umbrella to create a holistic security platform that includes people, process and technology.
People: we focus on the “human factor”, using engaging, structured, content to raise cyber awareness and engender “active defence” behaviours.
Process: we support the development and management of user security awareness plans, monitor user compliance and Key Performance Indicators and embed cyber security as an intrinsic part of the corporate culture.
Technology: we scan and isolate malicious attachments and email content and provide system administrators with “one-click” management across the enterprise.
We cover all phases of email threats with unique patent-pending solutions each of which is designed for that specific phase of the email attack chain and thus can stop an email-based attack even before it propagates.
Phishing: Avoiding the growing threat to business data
Email phishing is becoming more sophisticated and targeted. How can firms avoid being caught out?
What are the common challenges in the cyber security space?
The incredible speed of evolution in technology pave the way for the presence of next-generation cyber attacks. It is a common challenge for cyber security companies to track these next-generation cyber threats before they cause a breach.
However, to summarise some of today’s important security challenges:
- Ransomware: these attacks are the most threatening and disruptive tactics used by cybercriminals today. When they are successful, criminals seize the target computer or even the entire network. If the victim pays a ransom, then he/she may hopefully get the computer and system back, however evidence suggests they will be attacked again and again.
- The Internet of Things (IoT): smart devices radically reshape our lives. However, these devices are particularly vulnerable and can be easily exploited with various attack techniques.
- Internal threats: it can occur when employee within an organisation with authorised access cause harm to the organization’s critical information or systems – this is often due to human error rather than a deliberate act. Insider Threats include third-party vendors, contractors and partners.
What are the biggest mistakes a company can make regarding security?
- Assuming they’re not a target for cybercriminals.
- Not investing time and effort into training employees in cyber awareness.
- Relying solely on anti-virus technologies.
- Networks and the target locations are too vast. Ignoring updates and recommended patches is a critical issue.
- Not developing a holistic cyber resilience approach across the organisation.
Provide your best practice advice/top tip for effective cyber security?
For effective cyber security, companies need a cyber-resilient solution that includes people, process and technology factors. When technology fails to prevent attacks, qualified/trained employees are the last line of defence to protect your company. Processes are important to track the attack trends, update the gaps in your defence technologies, and train the employees. Achieving automated incident response will greatly reduce the impact of an attack on your organisation.
Phishing attacks can AI help people provide a fix?
What’s next?
Phishing forms the basis of more than 91% of breaches. 95% of successful cyber-attacks start using the same email-based method. Phishing is the preferred method of attack for high-threat actors due to its effectiveness.
It takes an average of 146 days to identify a breach and a further 82 days to contain it. Recent examples include the WannaCry ransomware outbreak, where the NHS faced a recovery bill in excess of £92M to restore systems.
In addition to the risk of compromise, there is the additional concern of non-compliance. GDPR and NIS regulations impose significant fines if an organisation’s lack of security controls lead to a breach of personal data or non-availability of critical services.
Keepnet Labs solution delivers a full-spectrum approach to mitigating phishing risk by:
- Analysis of phishing attacks using Artificial Intelligence and third-party integration for identification, notification and deletion of suspicious mails;
- Safely simulating phishing attacks using a broad range of real-world models;
- Automating malicious email management through “one-click” removal;
- Proving education modules with third-party training platform integration;
- Supporting user training and recording of training outcomes and compliance;
- Delivering integrated cyber-intelligence reporting; and
- Cloud and on-premise implementation options.