According to figures from Statista, the global cyber security market is forecast to grow 80% to $248.3bn by 2023, from $137.6bn in 2017. Needless to say, cyber security has become big business.
Nowadays, vendors have to clamour over one another to distinguish themselves as the most comprehensive solution available.
At the same time, the market is becoming increasingly fragmented and niche. On the face of it, it also appears more sophisticated. Gone are the days when enterprises were being sold a simple firewall or anti-virus; nowadays, vendors are boasting of futuristic solutions such as AI-based threat detection, automated incident response and predictive threat intelligence.
Enterprises, no doubt, are being spoilt for choice. However, while competition is typically regarded as beneficial to consumers, the market now feels overly complicated. Enterprises are struggling to judge which solutions are right for them.
Moving beyond self-evaluations
As Simon Edwards, founder and director at SE Labs, put it, when he spoke with Information Age recently, “In reality, there isn’t a great deal of resources out there to make good comparisons, and too often it just comes down to price in the end.”
Furthermore, too many vendors are making promises that are hard to substantiate.
“Aggressive and misleading marketing from some security vendors has made it very difficult for procurement departments to make good buying decisions. ‘Smoke and mirrors’ is a common term used by concerned customers considering where to spend their often very large budgets,” he said.
Tech Nation’s cyber security cohort: SE Labs’ company profile
Edwards argued this is frustrating for both enterprises and vendors. “Enterprises are left feeling unsure if they’re buying comprehensive protection or snake oil. While good cyber security vendors, who have great products and services that work, are being written off.”
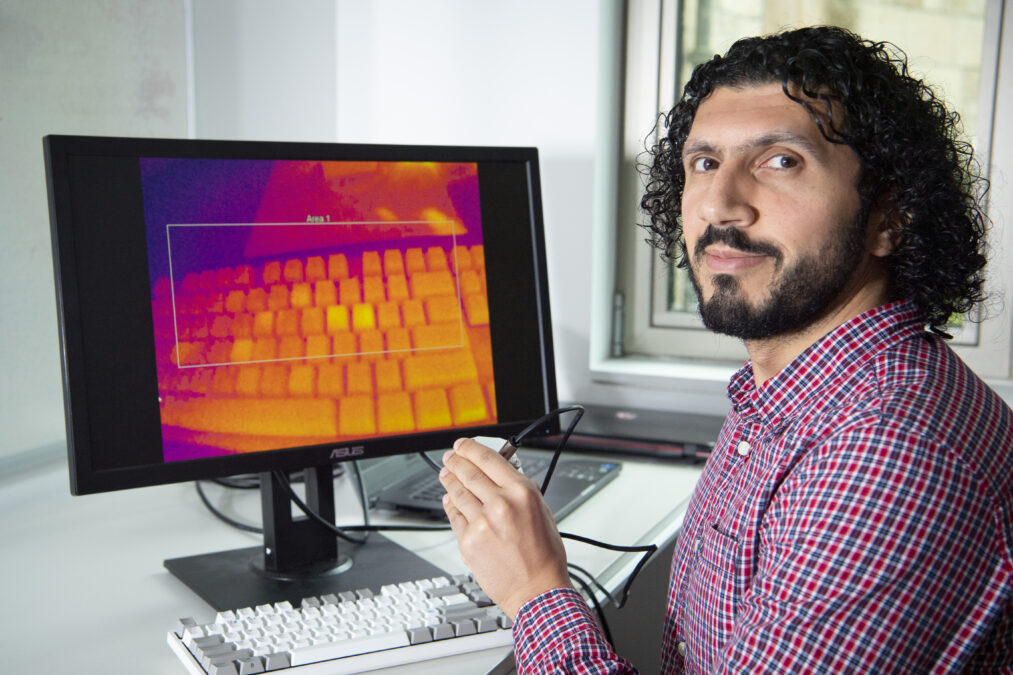
While marketing departments appear to have no doubt about the effectiveness of their product, according to Edwards, the fact is that without in-depth testing no-one really knows whether or not an Endpoint Detection and Response (EDR) agent can do what it is intended.
“It’s really important to test the products using what the industry calls the full attack chain, this means taking the attack from the very beginning to its logical conclusion,” he said.
Third-party validation
Edwards argued that security vendors themselves require third-party validation and data to help identify weaknesses in their products, which their internal testing is unlikely to identify.
“They’ll only test what they know about, while an independent tester will introduce new ideas,” he said. “They may see particular challenges with social engineering attacks, which are hard for automated computer-driven products to detect and prevent.
“Malware also remains a challenge, despite many bullish and misleading marketing claims from product vendors that ‘anti-virus’ is dead and the main threat is from nation-state attackers who ‘hack’ rather than use malware.”
Stranger emails: rethinking anti-phishing solutions in the enterprise
According to Edwards, third-party validation is also useful for enterprises as well. “They’re the ones spending millions on this. And while they, of course, have teams that can asses vendors, they are often limited. Generally what happens is they do their testing, but they involve the vendors themselves — this is called a proof of concept. Of course, there will be biases in these tests.”
According to Edwards, third-party validators can be brought on board to do another test that can substantiate the findings.
“The test will either agree with their results, in which case they can go to the board and say they are making a solid decision, and that’s great, or the test will conclude that they’re not going to get the value they were told to expect.”
SE Labs is part of Tech Nation Cyber — the UK’s first national scaleup programme for the cyber security sector. It is aimed at ambitious tech companies ready for growth.
 Tech Leaders Summit
Tech Leaders Summit
On 12 September, Information Age will once again host Tech Leaders Summit at the Royal Lancaster Hotel, London. This year, speakers at the UK’s most innovative tech leadership conference — including the CTOs of RBS and Ofcom and Sarah Burnett from Everest Group — will help dissect subjects, such as intelligent automation, emerging tech, agile and cultural transformation. With plenty of opportunties to network throughout the day, this event is not be missed. To find out about the latest innovations and how to lead your organisations and customers through the disrupted era, register here.