Biometrics is the heart of identity verification — a market that is continually expanding.
Today, businesses and consumers are moving away from passwords and towards biometrics: face, voice, iris, fingerprint and even DNA. In an online world faced with fast-emerging and increasingly dangerous cyber attacks, biometrics are creating security, in a seemingly insecure world.
But why are business’ choosing to verify their customers with face biometrics over any others?
The face is the sole biometric that links an individual to a legal identity. A face is found on a government-issued identities: passports, driving licences, identity cards, etcetera.
How facial recognition could save insurance companies billions
A new system based on deep learning AI could significantly reduce claims fraud. Read here
The problem with facial biometrics
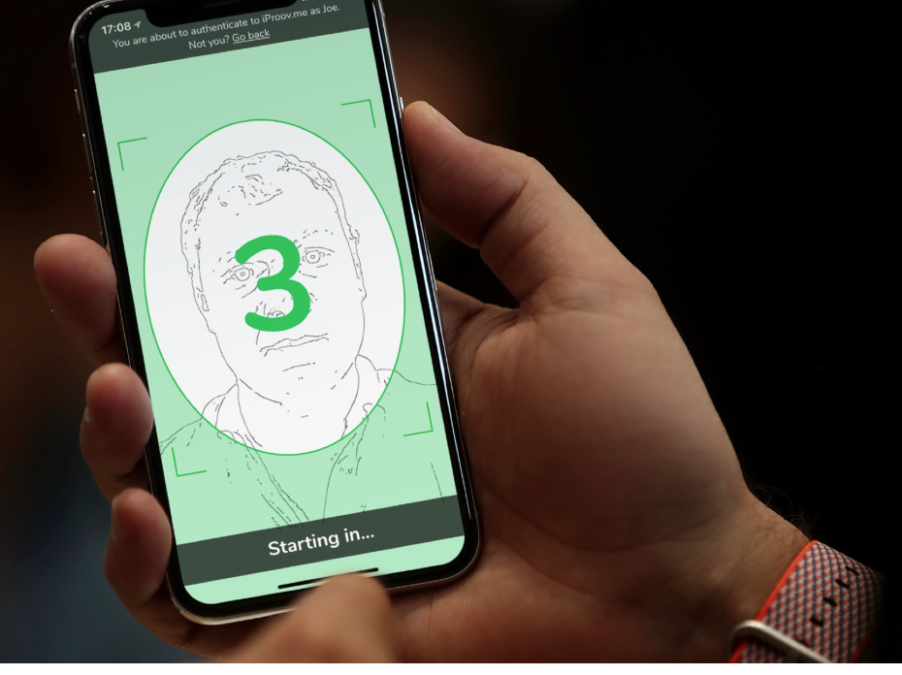
But there is a “problem at the heart of facial biometrics,” says Andrew Bud, founder and CEO of iProov — the company that specialises in remote biometric authentication.
How can a businesses tell if a user is a “genuinely present person, as opposed to a physical or digital copy” asks Bud?
This isn’t just a case of verifying an individual matches an ID document; in fact, face matching is now virtually a commodity. Rather, the fundamental challenge of face biometrics is guaranteeing a user is a real person and that they are genuinely present at the moment in which they are interacting with the service.
“We have to assure that, in a changing threat landscape,” Bud continues.
Authentication vs identification: Understanding the technology behind face ID
Genuine presence
Genuine presence is a very hard problem — it’s much harder than checking someone is who they say they are.
A person’s face is not secret. With the advent of social media, a hacker doesn’t have to steal a face.
An individual’s face is a public credential and therefore, the real problem is: how do you tell whether you’re looking at a genuinely present face or a copy of the victim’s face? As organisations continue to adopt biometric authentication, businesses’ must be able to detect fraudulent identities.
iProov has made solving this conundrum their mission.
Bud explains: “Our flashmark technology uses the screen of the user’s device to illuminate the person’s face with a rapidly changing sequence of colours. And while that’s happening, we stream video of their face back to our servers. From the way that the light reflects and interacts with the face, we can tell whether it is a live skin-covered three-dimensional human face shaped object or not. On top of that, the sequence of colours is different each time, it’s like a multi-coloured encrypted timestamp.
“We look at these sequence of colours reflected from the person’s face and if it’s the correct sequence, then we know that they’re present now. But if it’s the wrong sequence, we know we’re looking at a recording or a pre-created fake video.”
Facial biometrics is worthless without genuine presence assurance
Facial biometrics adoption
Biometrics have been adopted by some of the largest and most demanding customers in the world. For example, the UK Home Office is using iProov technology for their EU Settled Status application.
“On the last weekend of March alone, 50,000 people used the iProov-powered application,” says Bud. And, he proudly points to the fact over 80% of users said that it was easy or very easy to use.
Arguably, usability is the fundamental determiner of the success of any technology.
The Department of Homeland Security in the United States is another customer of iProov. Bud comments that iProov was “the first ever non-US company to receive a contract from the Science and Technology Directorate’s Silicon Valley Innovation Programme.”
“We’re working to help low-risk travellers cross the land border more quickly and at lower cost. And we have a number of banking customers live in Europe, including ING and Rabobank in the Netherlands who are using our technology.”
Identity
There are three elements to identity — each is used to assemble and store a series of attributes about a person that together makes up their identity.
With all of them, you need a secure way of passing the relevant attributes from the store to the part that you need to rely on. And then you need to authenticate the user’s right to assert those attributes: to say those are my attributes, use them.
Scaling facial biometrics
To scale, facial biometrics technology should be delivered as a Software-as-a-Service (SaaS) hosted in the cloud.
“All of the functionality should be provided via SaaS servers,” confirms Bud. In iProov’s case, these are hosted in Microsoft Azure and delivered into enterprise mobile apps and for desktop purposes, into web pages.
Integration and deployment must be an incredibly simple process — it’s the solution’s job to do all the heavy lifting.
Universal
Facial biometrics, similar to an ID card, will become universal.
As consumers move into a world of unsupervised self-service, facial verification will become ubiquitous. As this happens, genuine presence assurance will be absolutely obligatory.
The future of self-service is customer-led automation — Gartner