Bond films have shown us some of the most quirky technology modifications to cars from the Siri-like voice assistance, Homing Device, and even an invisibility system when fleeing a villain.
But for over a hundred years, cars have simply been machines of metal and motor with the single purpose of transporting passengers and cargo.
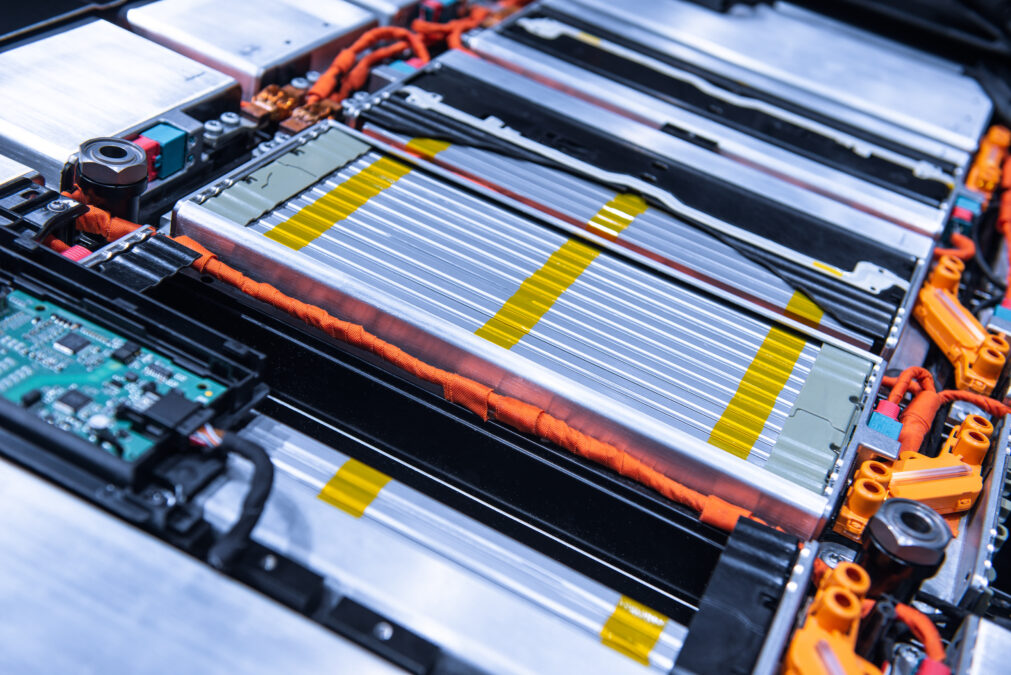
It’s only over the past fifty years that we’ve seen the car industry adopt electronics and IT to meet regulatory requirements for safety, emissions control, and to improve diagnostics. Notably we’ve seen this in the development of hybrid vehicles, plug-in electric vehicles and hydrogen vehicles.
Much as owners expect anti-lock brakes, airbags and seat belts as standard features rather than aftermarket or retrofitted options, today’s consumers demand digital security that is delivered unobtrusively with the vehicle.
The advanced smartphone can already unlock owner’s cars, check the status of batteries on electric cars, find the location of the car, or remotely activate the climate control system.
> See also: Connected cars are the future, but how far along the road are we?
In 2020, 250 million vehicles will be connected and fully packed with sensor technologies, according to Gartner.
And although most consumers aren’t quite ready to fully hand over control to the self-driving car and self parking car yet, as demoed by the likes of Google and other motor brands, we are already delegating a lot of our daily tasks to technology.
The future connected car will know what you are going to do during the day, and adapts to your lifestyle to reflect this. But as it is essentially an IT system on wheels it also needs to be secure from IT vulnerabilities, just like your PC but it also needs to adapt to the external environment such as extremes of temperature, dust and damp.
The lifecycle of a connected car
Before a new connected car owner first sits behind the steering wheel, a number of preparatory steps for final delivery should be accomplished. Such as including updating electronics with the most current software and firmware and setting up access with maintenance and support services, as well as services like traffic and weather feeds.
On one hand, automatic updates can help close off security vulnerabilities and keep vehicle owners safe from electronic threats; yet, ironically, the mechanism that provides this capability, over the air updates, increases the vehicle threat surface.
During a vehicle’s in-service life, owners and operators may interface with a wide range of computing systems and computing services in support of maintenance, customer support or value-added services, such as satellite radio, etc.
These systems can contribute to security and privacy risks by exposing information or points of service access.
Finally, automobile manufacturers need to account for upgrades to cryptographic software and data during the in-service lifetime of connected vehicles.
To stay competitive and differentiated in the market, automakers have created open, scalable and flexible mobility services that are customisable.
They’re also paying attention to 'non-car owners' who opt for alternate mobility services like public transportation and car-sharing. Car2go, offered by moovel GmbH (a fully owned subsidiary of Daimler AG and a division of Daimler Financial Services AG), is a unique car-sharing service that allows members to rent vehicles by the minute and return them to open parking spaces in designated areas. The company is also introducing electric cars with recharging stations at convenient locations.
These types of programs offer a variety of benefits, such as using electric vehicles for short-distance transport is ecologically sound; keeping vehicles on the go as much as possible reduces long-term parking, a waste of precious urban real estate; and producing smaller vehicles to accommodate the many single-passenger transportation needs further supports vehicle density.
But this functionality comes with risks as hackers have demonstrated that they can display false telemetry on the dashboard, wrestle the steering away from the in-cabin driver and even apply the brakes or switch off the engine remotely when the vehicle is at high speed on a crowded highway.
Automobile manufacturers, dealers, mechanics and end users must adapt to new technological concepts and production methods, not just to ensure the safety, efficiency and comfort of automobile drivers and passengers, but also to ensure their privacy and data security.
They must continue to make safety a top priority, but must now include protection against computer incursions.
The integrity of the IT and production systems and the facilities themselves must be assured; if a control system is compromised by malware, the very machines designed to produce automobiles efficiently and with exacting standards can be coerced into introducing flaws into the final product.
The end result could be injury to the operators of the vehicles, brand reputation damage to the automakers, or theft of intellectual property and practices.
Assembly plants contain standard IT systems, like servers, workstations, networking equipment and storage devices. They also operate industrial control systems.
While there are well-understood security controls for standard IT systems, including authentication and access control, firewalls and endpoint protection, industrial control systems often run on antiquated or esoteric operating systems, contain hard-coded administrative credentials, or are simply not well understood by IT professionals.
Nevertheless, industrial control systems need to be protected from electronic subversion to avoid threats, such as Stuxnet, a 500-kilobyte computer worm that infected the software of at least 14 industrial sites in Iran.
To secure production assembly, automakers should: understand the functions, applications, interfaces and protocols associated with each system used in manufacturing.
In effect, keep a current asset inventory of critical cyber assets, including system owners, authorised roles and users, and interaction with other information system assets; have a codified security policy that guides implementation and maintenance of critical assets.
The security policy must take into account availability of systems and data, as well as integrity and confidentiality; implement access and security controls to protect the equipment and data, guided by the security policy; and instrument systems to monitor events and perform analytics to detect not only failures, but also suspicious activity potentially indicating a security threat.
Encryption can also help prevent hijacking and spoofing of control commands. Here are a couple of tips and tricks to adopt:
Analyse data patterns. With sophisticated attacks, it’s not always possible to prevent malicious activity. However, instrumenting and analysing data patterns from individual cars and fleets can detect anomalies that may be signs of coordinated attacks.
By generating meaningful events in a format useful to big data solutions, analytics can identify suspicious activity before the vehicle’s systems are compromised and the attacker causes damage.
> See also: How driverless cars can and will be hacked
Apply analytics solutions: Apply big data analytics to identify attempted attacks on vehicle control and telematics systems and potential fraud across the entire lifecycle of the vehicle (insurance, tax, parts) preserving the safety and privacy of the driver.
IBM has worked with the top manufacturers of automobiles, automotive components and services around the world to understand the risks and threats and to mitigate fraud to instrumented, connected, intelligent vehicles, so we can devise practices to help ensure safety and security.
The result is a security model that follows modern vehicles from rough sketch to scrap metal, which we call design, build, and drive.
Looking to the cloud, Gartner recently cited that One-third of consumer data will be stored in the cloud by 2016. In addition in-vehicle software will be updated over the air through cloud connectivity.
A cloud-based service can help automakers turn driver and vehicle data into actionable insights for predictive vehicle maintenance, real-time diagnostics on engine trouble, and to guide drivers to the most efficient traffic routes.
By 2020, we see that 90% of new cars will be equipped with extensive connectivity services- Let’s make sure we’re ready to take on the hackers.
Sourced from Doug Clark, IBM Cloud UK&I