Malware and cybercrime: a match made in heaven. But it's the malware that makes it particularly difficult to prevent. Between viruses, worms, adware and spyware, the IT manager has a near impossible task of data protection through blocking, routing, zoning, and scanning for threats and weaknesses in the company's network and software systems.
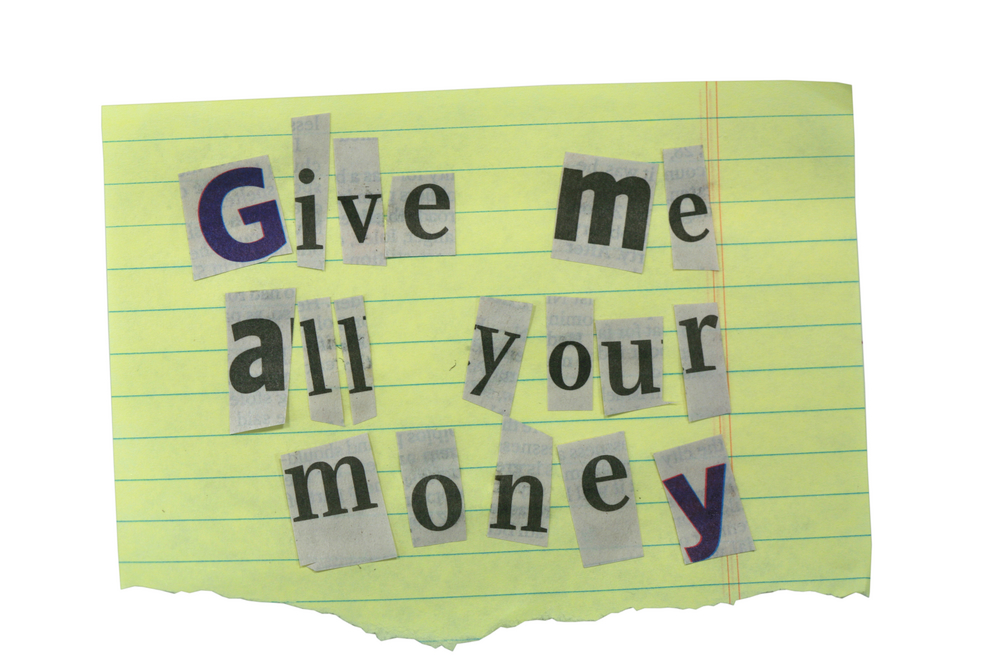
However, ransomware can be especially debilitating, depending on the strength of the attacker's experience and the strength of your negotiator. Such an attack basically involves a program being installed, through a worm or virus that carries the program, on a computer and then locks it down thereby suspending any activities on the computer.
Attackers then have access to your full system and can use this information to their advantage. No one is able to operate or bypass it unless they respond to the demands displayed on the screen – usually for vast sums of money.
> See also: Apple has been targeted by ransomware for the first time, so how big is the risk to business?
Attackers don't discriminate
It isn’t just large private organisations with vast sums of money that can fall victim to these kind of attacks. This was recently demonstrated when the Hollywood Presbyterian Medical Centre in the US was caught unaware and held to ransom.
Unfortunately, this affected operations at the hospital for more than a week while officials scrambled to collect the bitcoins that were being extorted. News reports are unclear whether it was for the value of $17,000 or $3.4 million, but regardless they had to pay.
Complying with attackers' demands is usually the path of least resistance, and has a fairly predictable result. Unfortunately, you end up on the losing side of this little power play.
So a far better approach would be to even out the odds between you and the attacker by being prepared. Besides the blocking, routing, zoning, and scanning for threats, an effective data protection solution will save the day.
A better data protection solution
In order to ensure your system is better prepared for the threat of ransomware, the first step is to implement regular backups of your company’s data. By keeping regular backups of your systems, with short intervals between backups as is practically possible (i.e. having a low Recovery Point Objective/RPO), a recent copy of your data will always be available.
Consider a cloud-based backup solution if you don't want to incur the higher costs for the purchase and maintenance of data storage. Otherwise, just make sure you keep the latest copies of your most important information on site.
> See also: Ransomware now costing big businesses in downtime
However, having the backups is only as good as being able to restore them. Proper data protection also means that you'll need the right infrastructure in place to facilitate data recovery as quick as possible (i.e. a low Recovery Time Objective/RTO). A cloud-based data protection solution will also ensure that your data is kept off-site and out of harm's reach.
Whether your backups are kept on the premises or off-site, it should become regular practice to test your data protection solution for integrity and completeness. This will ensure that when the time comes, you'll have the right data at your disposal and you'll know that your data recovery will be more effective.
Sourced from Paul Evans, CEO, Redstor