Information Age has partnered with Tech Nation to help explore 20 of the UK’s leading cyber security scaleups.
Tech Nation Cyber is the UK’s first national scaleup programme for the cyber security sector. It is aimed at ambitious tech companies ready for growth.
In a series of 20 company profiles, we will be introducing you to the cyber security scaleups that make up Tech Nation’s first cyber cohort.
3. iProov
All answers provided by Aarti Samani, product and marketing director at iProov
What does your company do?
iProov assures genuine human presence in digital environment.
https://www.youtube.com/watch?v=d4m0YptB4dg
How do you differentiate from your competitors?
iProov is the only genuine presence assurance company in existence. We have developed and patented flashmark technology that allows users to authenticate securely without friction. It is a passive authentication solution with an intuitive user interface.
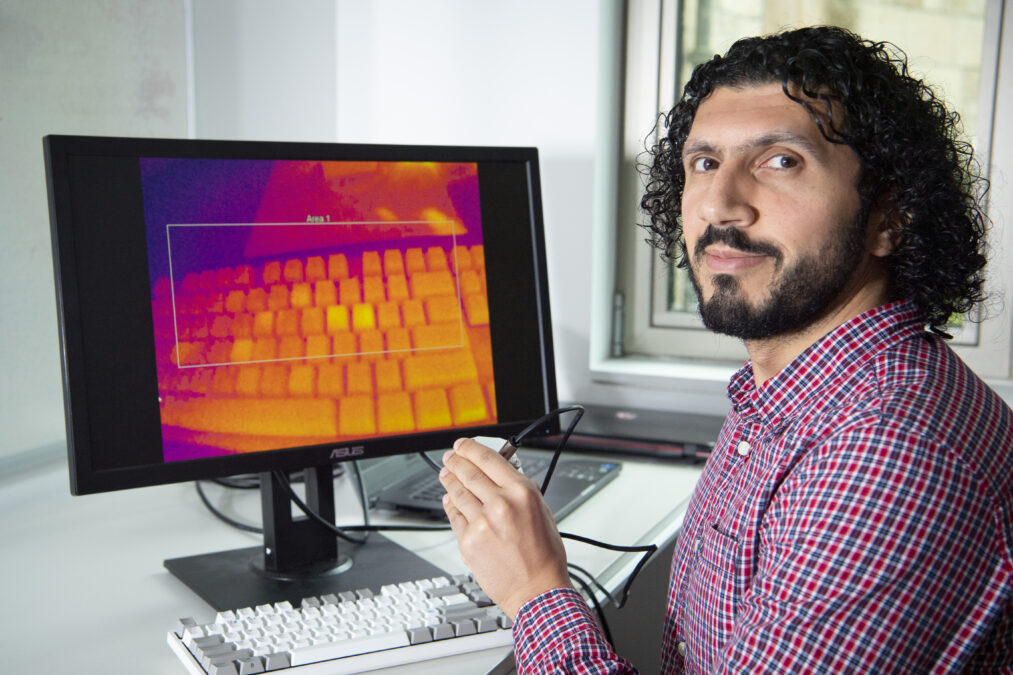
Facial biometrics: assuring genuine presence of the user
What are the common challenges in the cyber security space?
The biggest threats in cyber security are from deep fake videos and replay attacks. These type of attacks are easy to create at scale and difficult to detect by even some of the most sophisticated systems. iProov’s genuine presence assurance can reliably detect and stop both of these as well as all known attack vectors.

What are the biggest mistakes a company can make regarding security?
Security is an arms race. A company cannot be complacent and claim that their solution will never be compromised. Attacks and attackers are getting more and more sophisticated, and security vendors need to be able to respond to these quickly and effectively.
Provide your best practice advice/top tip for effective cyber security?
Continuously monitor activity to detect threats in near real time and prepare to respond rapidly. Do not rely on fixed, unmonitored processes.
What’s next?
1Billion iProov transactions!