Information Age has partnered with Tech Nation to help explore 20 of the UK’s leading cyber security scaleups.
Tech Nation Cyber is the UK’s first national scaleup programme for the cyber security sector. It is aimed at ambitious tech companies ready for growth.
In a series of 20 company profiles, we will be introducing you to the cyber security scaleups that make up Tech Nation’s first cyber cohort.
7. My1Login
All answers provided by Mike Newman, CEO at My1Login.
What does your company do?
My1Login is the UK’s most secure, most widely-compatible, award-winning enterprise Identity & Access Management solution that enables organisations to mitigate password-related cyber-security risks, control user identities and help meet critical compliance obligations such as GDPR.
My1Login’s IAM solution solves the problem of weak passwords and practices, enabling organisations to control user access and centralise identity through Single Sign-On. Its SSO integrates with all app types – web apps, mobile apps, flash apps, virtualised apps, and even legacy, thick-client apps and mainframes.
My1Login can also be used to prevent phishing by centrally creating password policies that automatically update user passwords on third-party applications. These passwords can then be hidden from users on the My1Login system so users are able to log into the application, but are unaware of the password for it – and if they don’t know the password, how can they be ‘phished’ for it?
My1Login’s auto-detection of applications further reduces the attack surface by removing the blindspots created by Shadow IT.
My1Login is a UK leader in protecting against enterprise cyber security threats through its Identity and Access Management solution.
Identity and access management — mitigating password-related cyber security risks
How do you differentiate from your competitors?
My1Login differentiates from competitors for five main reasons:
1. My1Login’s encryption architecture is fundamentally more secure than the majority of competitors due to use of client-side encryption, rather than server-side. My1Login only store encrypted data with the keys remaining securely inside the perimeter of the customer’s network meaning even My1Login cannot access customers’ data.
2. My1Login provides an optional on-premise, back-up cache.
3. My1Login are the most widely-compatible solution, providing authentication into all application types ranging from web through to legacy Windows desktop executables.
4. My1Login eliminates phishing since the solution can automatically update passwords on 3rd party applications then hide these from end-users. If employees don’t know any passwords, how can they be phished for them?
5. My1Login proactively detects Shadow-IT and enables business related apps to be integrated with Single Sign-On with a one-click policy decision.
My1Login is a wholly-European organisation eliminating concerns around data and vendor sovereignty for European businesses.
What are the biggest mistakes a company can make regarding security?
The common theme is that of compromised identities. Verizon’s Data Breach Investigations Report 2017 confirms this, with their research finding that 81% of hacking-related breaches involved weak or stolen passwords.
The trend towards SaaS is moving enterprise identities outside the traditional corporate infrastructure, creating the challenge of securing access to applications that sit outside the organisation’s direct control.

What are the common challenges in the cyber security space?
The number one mistake organisations are making is leaving passwords and identities in the hands of employees. The people least interested, and least equipped to manage the security of access to critical applications — the end-users — are being asked to know what strong passwords are, create these strong, high-entropy, unique passwords, remember them and then regularly change them. It’s an impossibility for end-users to manage access to dozens of apps without introducing weak practices. It is for this reason that the majority of data breaches are due to compromised identities and passwords.
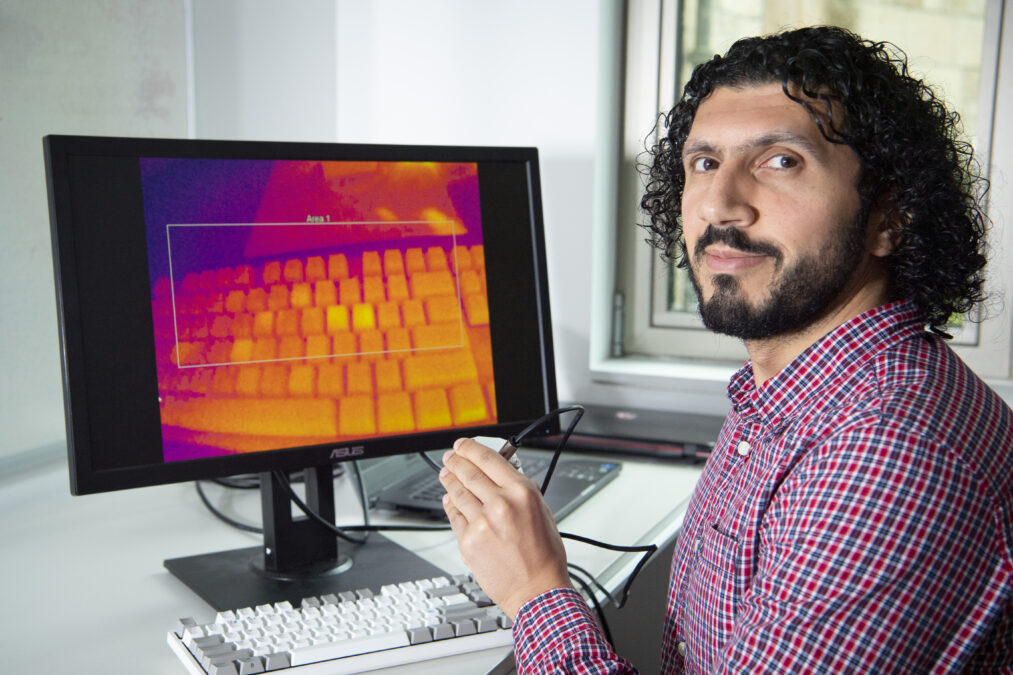
Facial biometrics: assuring genuine presence of the user
Provide your best practice advice/top tip for effective cyber security?
Organisations should take back control of user identities, by leveraging identity and access management solutions that remove the cyber-security risk associated with users creating, managing and using passwords. The majority of data breaches are due to weak, end-user password practices so removing the need for end-users to manage these identities eliminates this cyber risk whilst improving efficiency. As a convenient by-product, user password fatigue and frustration is also addressed.
What’s next?
Given the pervasiveness of biometrics on user mobile devices, we’re likely to see these being integrated more with access to corporate applications and services essentially moving towards a Bring Your Own Identity (BYOI) model. We’re also likely to see this type of authentication complimenting enterprise IAM solutions to bridge identities and access seamlessly across applications that harness either legacy and standards-based authentication methods.
My1Login is part of Tech Nation Cyber — the UK’s first national scaleup programme for the cyber security sector. It is aimed at ambitious tech companies ready for growth.